Cybersecurity Modules
Keplersafe Modules
Modules for Protecting Endpoints
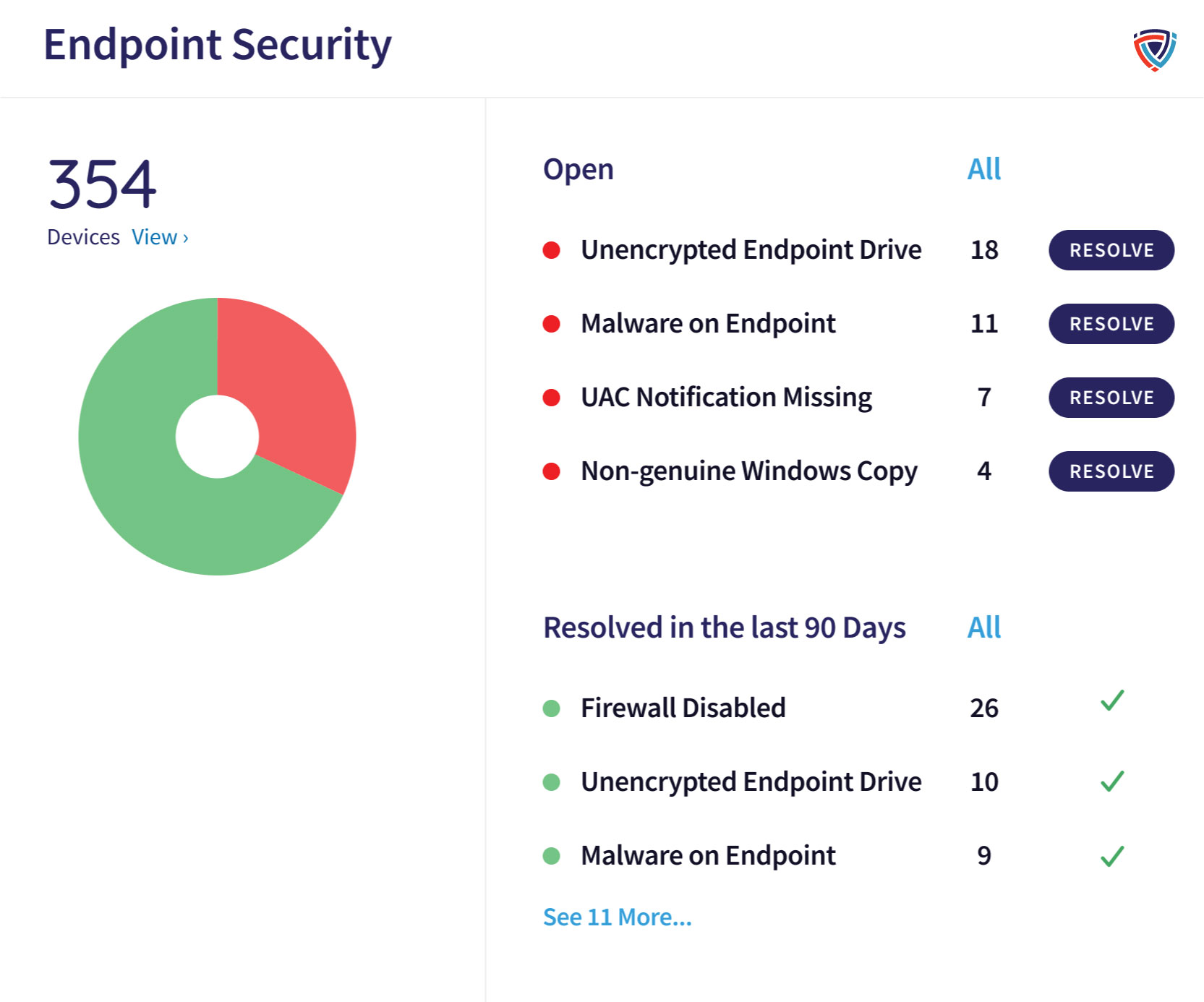
Endpoint Security
Endpoint Security is the core endpoint module in Keplersafe.
Capabilities:
- Device Posture: Apply policies to users or groups and determine the remediation action for vulnerabilities.
- Next-gen Antivirus: Advanced threat protection (ATP) analyzes both static files and running processes for anomalies.
- Allow/Block Lists: Create lists of files, folders, and processes to allow or block on your protected endpoints.
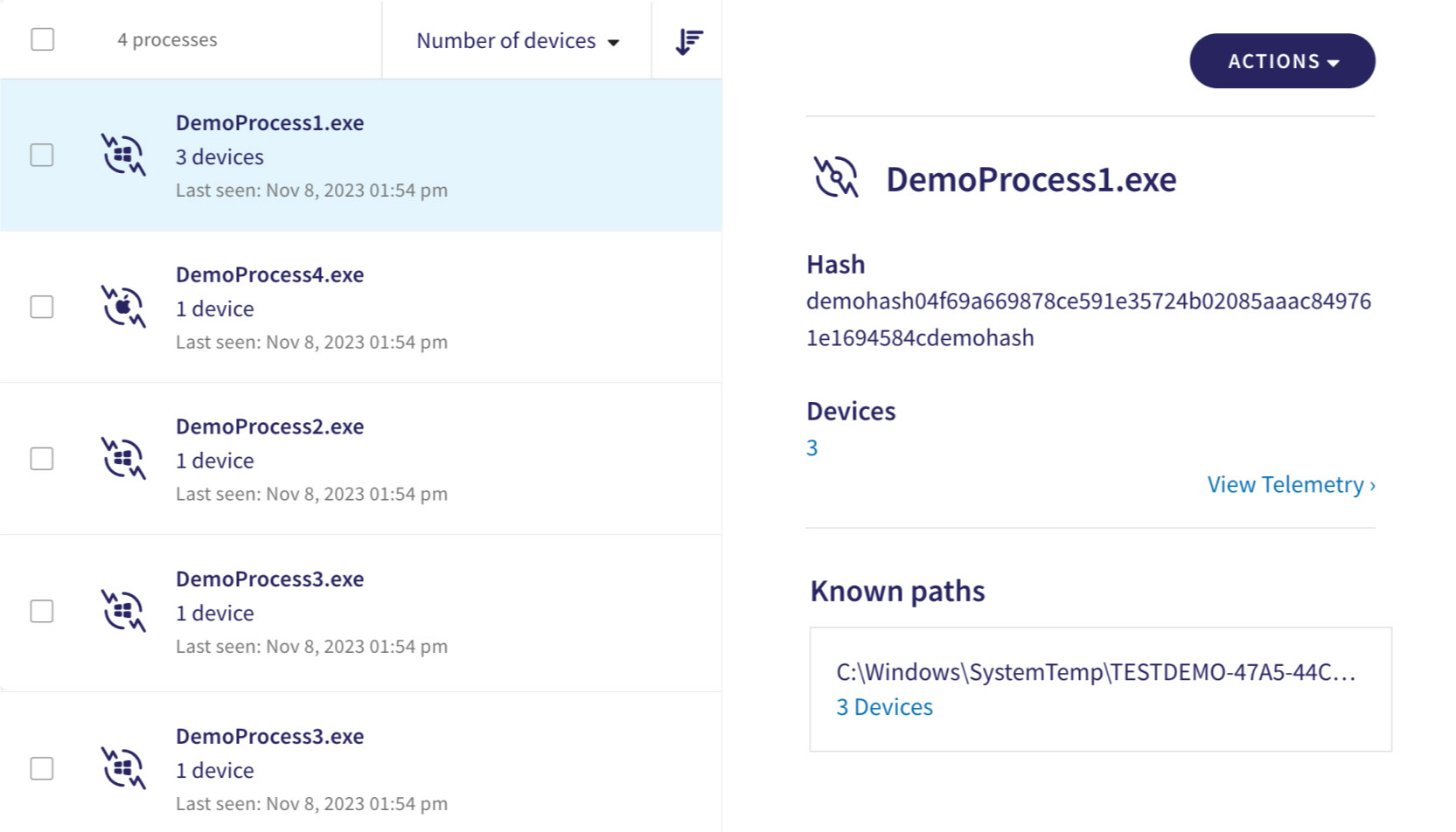
Endpoint Detection and Response
The Endpoint Detection and Response (EDR) module extends your ability to handle incidents as they occur. You can remediate quickly to prevent further damage from known and unknown threat sources and to conduct post-breach analysis.
It continuously monitors endpoint devices and presents these findings in clear, easy-to-manage tabs from the Keplersafe dashboard. Filter through the data as needed, and receive remediation guidance and immediate response actions.
Capabilities:
- Enhanced malicious software detection
- Proactive isolation of infected devices
- Automatic remediation across endpoints
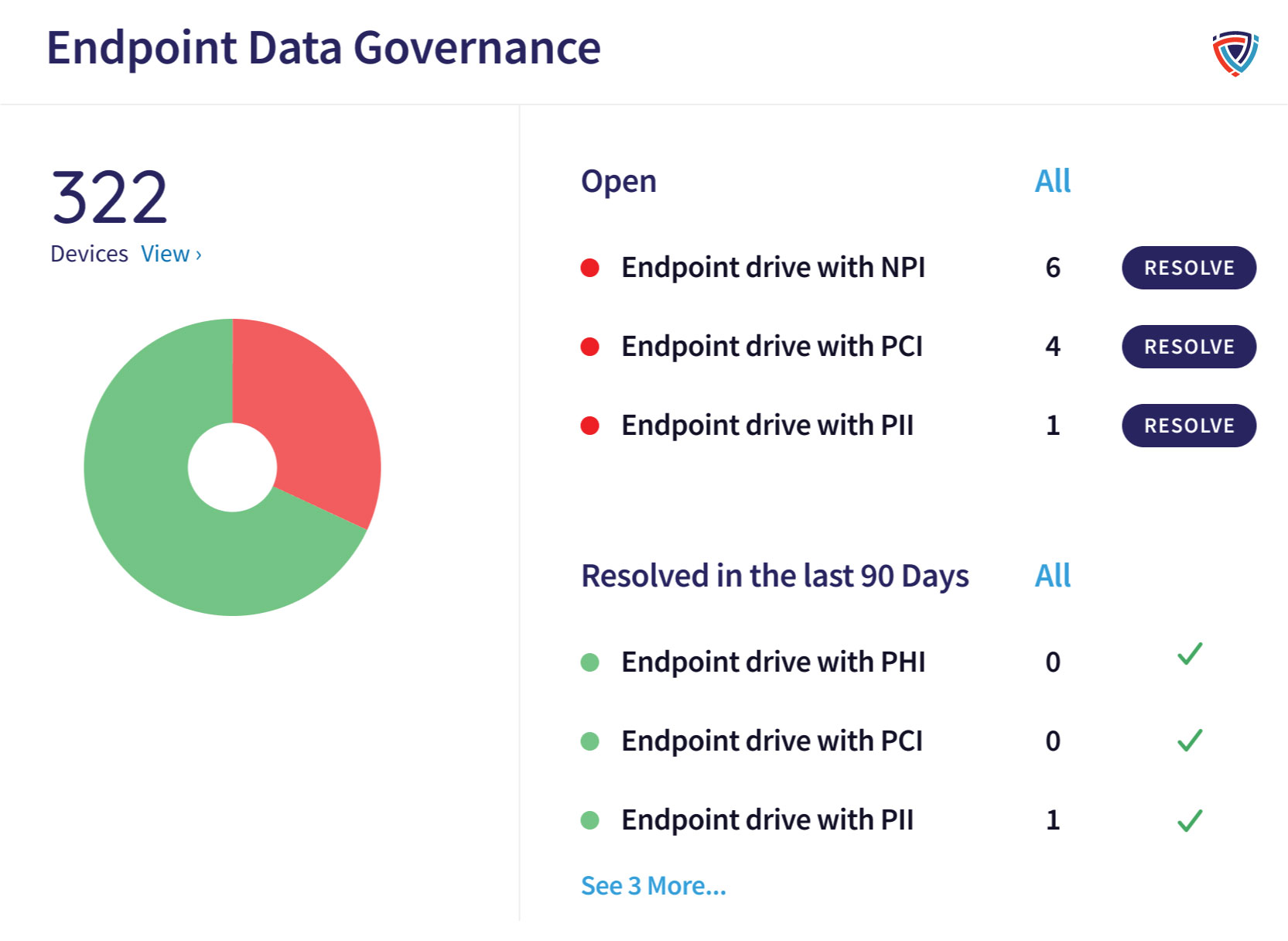
Endpoint Data Governance
The Endpoint Data Governance module protects sensitive data from unauthorized access, use, disclosure, modification, or destruction across endpoints.
To help ensure compliance with these regulatory standards, Keplersafe lets you remotely scan endpoints for:
Capabilities:
- PII (personally identifiable information)
- PHI (protected health information)
- PCI (payment card information)
- NPI (non-public information)
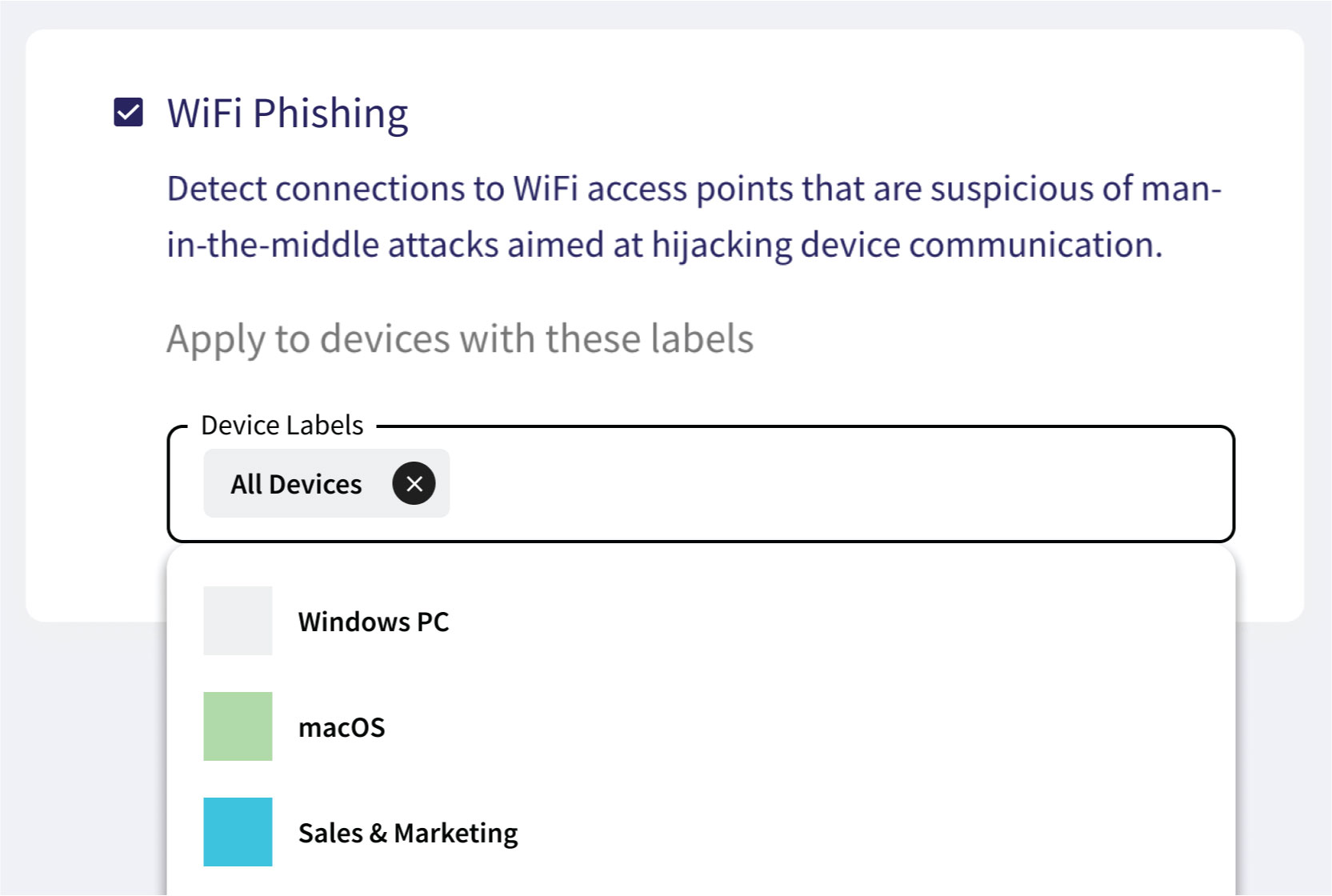
Wifi Phishing
The WiFi Phishing add-on guards endpoints outside the LAN (local area network) by preventing connections to suspicious WiFi access points. It works by detecting connections to WiFi access points that are suspicious of man-in-the-middle attacks aimed at hijacking device communication.
Protects:
- All devices in your workspace
- Specific groups of devices
- Remote/ traveling employees

Mobile Device Management
Mobile Device Management (MDM) enables you to manage iOS and Android mobile devices used by end users across your organization.
Capabilities:
- Report on mobile device activity and usage
- Remotely wipe data from compromised devices
- Enforce app policies across your company-owned devices
Modules for Protecting Email and Users
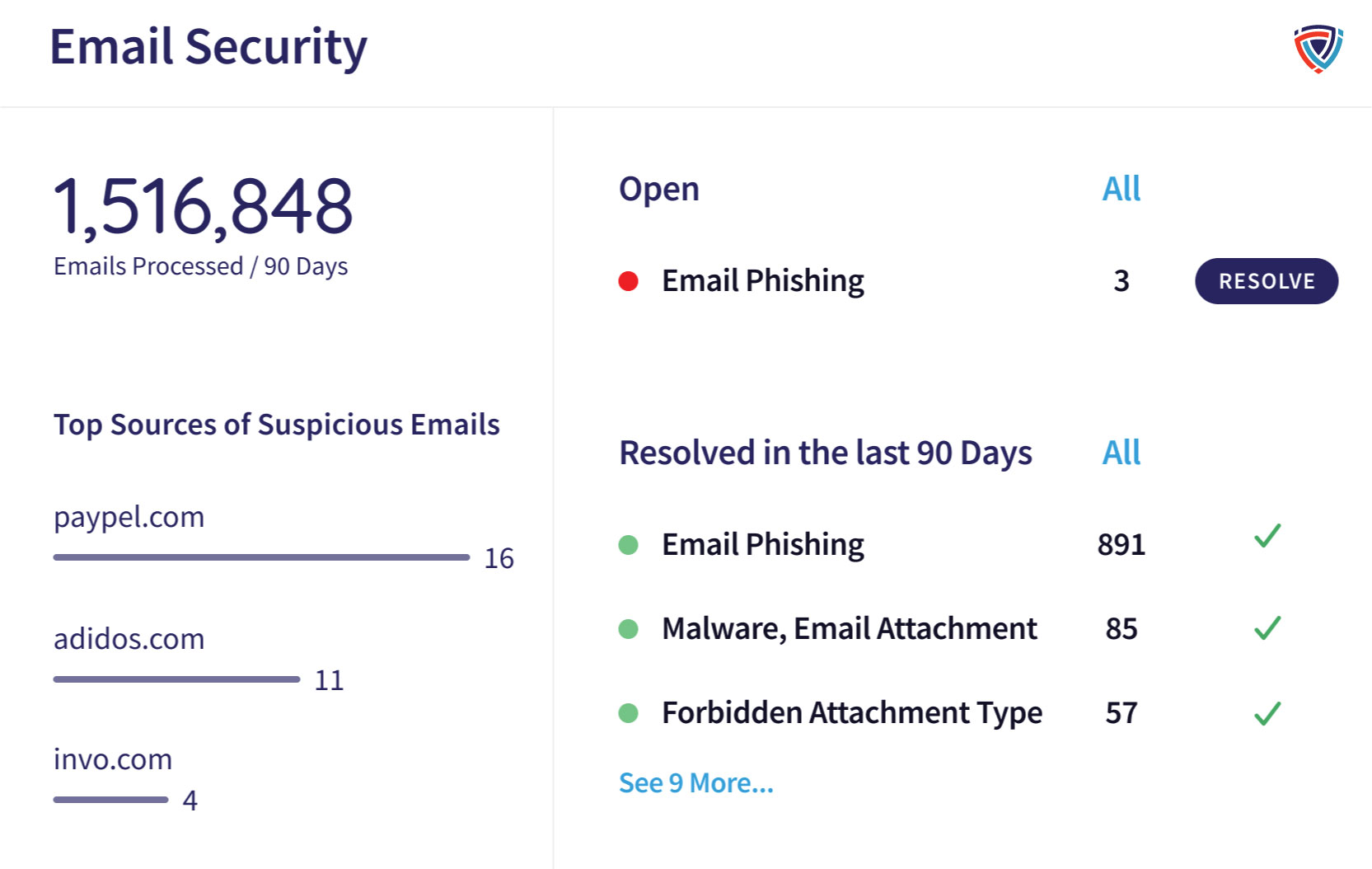
Email Security
Email Security is the core email module in Keplersafe.
Capabilities:
- Malware Scanning: Identify and quarantine emails with potential malware or ransomware attachments.
- Email Phishing Protection: Prevent threats from domain impersonation, spoofing, and other misleading phishing attempts.
- Allow/Block Lists: Create and maintain a list of individual senders or sending domains to allow or block from your business inboxes.
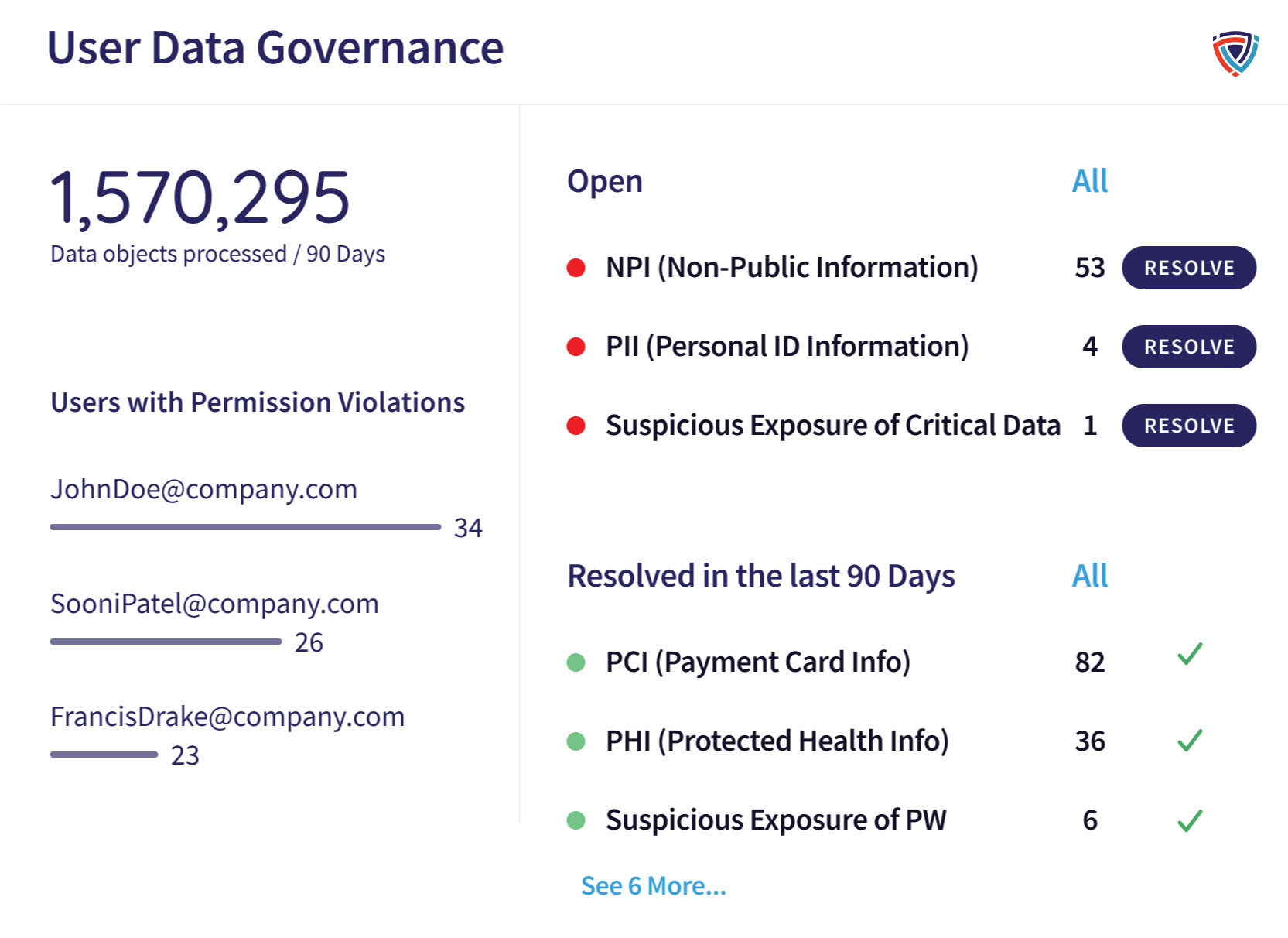
User Data Governance
The User Data Governance module helps administrators establish a data handling strategy. Make sure data is only being accessed by by authorized users and maintain compliance to strict regulatory standards.
This module scans emails for unauthorized disclosure of sensitive sensitive data like:
- PII (personally identifiable information)
- PHI (protected health information)
- PCI (payment card information)
- NPI (non-public information)
- Passwords
- Source code
- Certificates
- Custom keywords
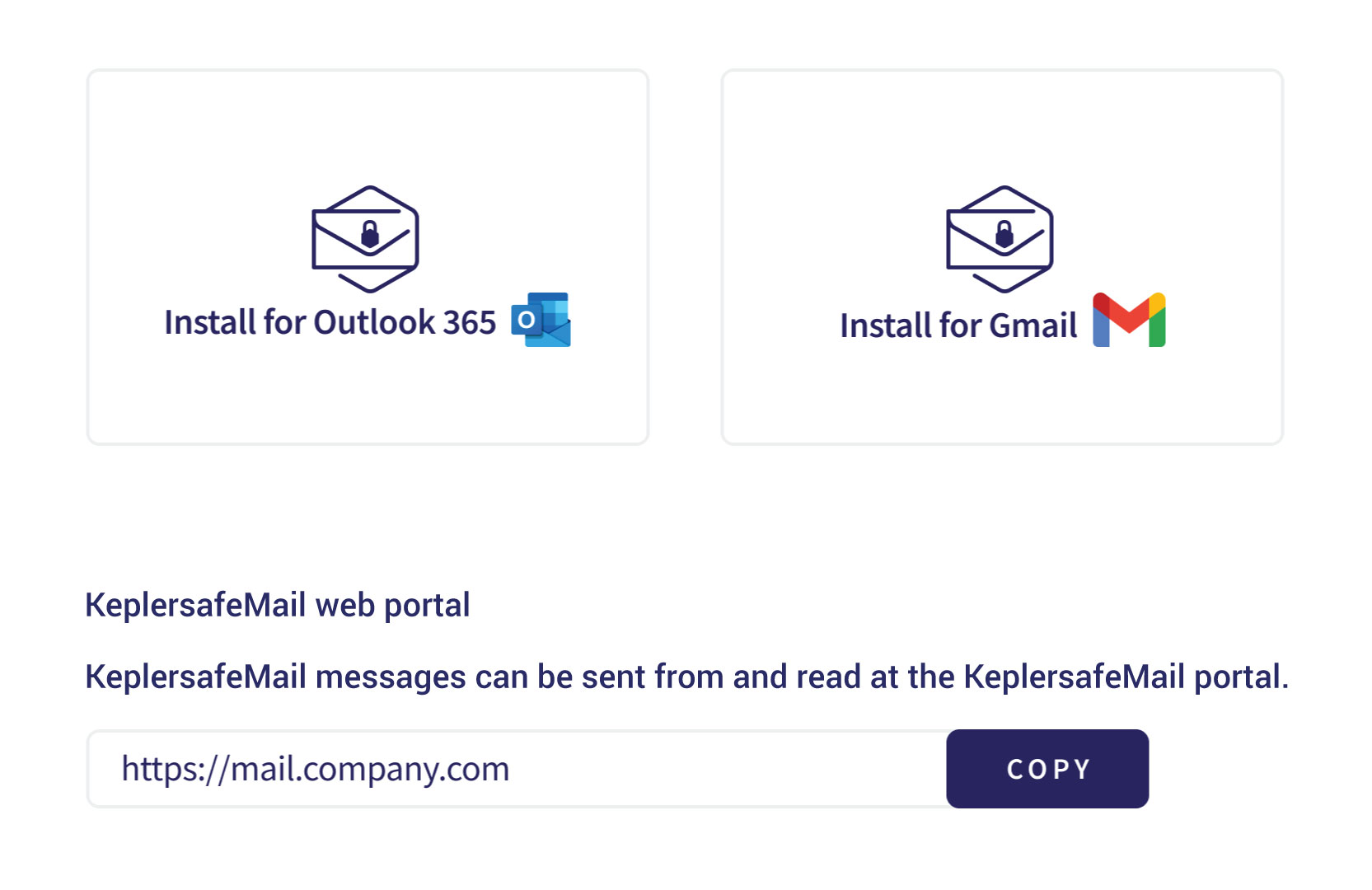
Secure Messages
The Secure Messages add-on lets you encrypt outbound emails. With this module, you can use a private key to ensure only the intended recipients to access emails.
Works with:
- Microsoft O365
- Google Workspaces
- Desktop email
- Mobile email apps
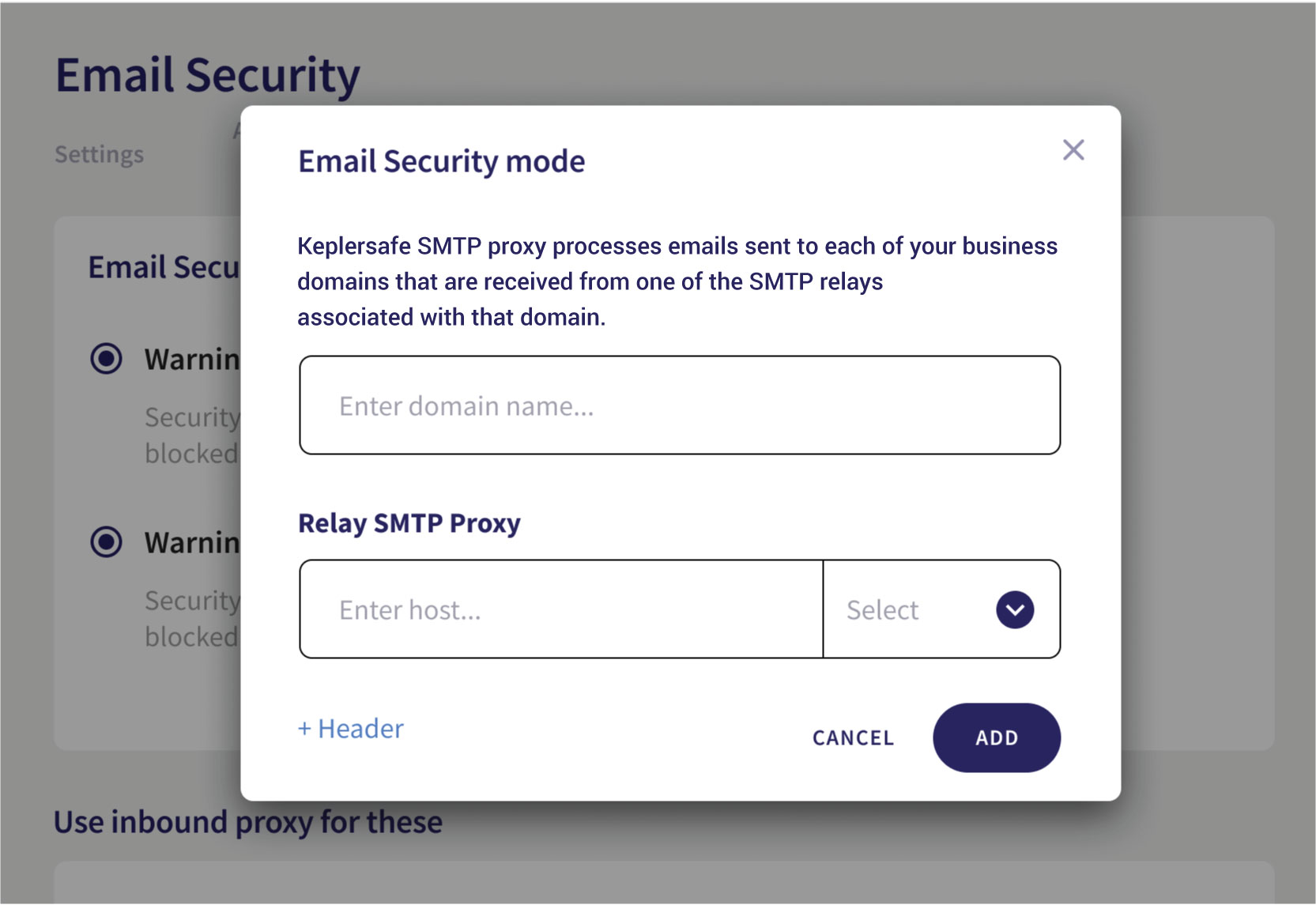
Inbound Gateway
The Inbound Gateway add-on is a proxy that provides real-time detection and protection for incoming emails. It lets you intercept inbound emails and inspect them, allowing only threat-free or trusted emails to reach recipients.
You can choose between the following for suspicious emails:
- Warning Only: Emails are not blocked but are marked with explanatory warnings for the recipients
- Block: Emails are blocked and can only be released from quarantine by workspace administrators
Modules for Protecting Network and Cloud Environments
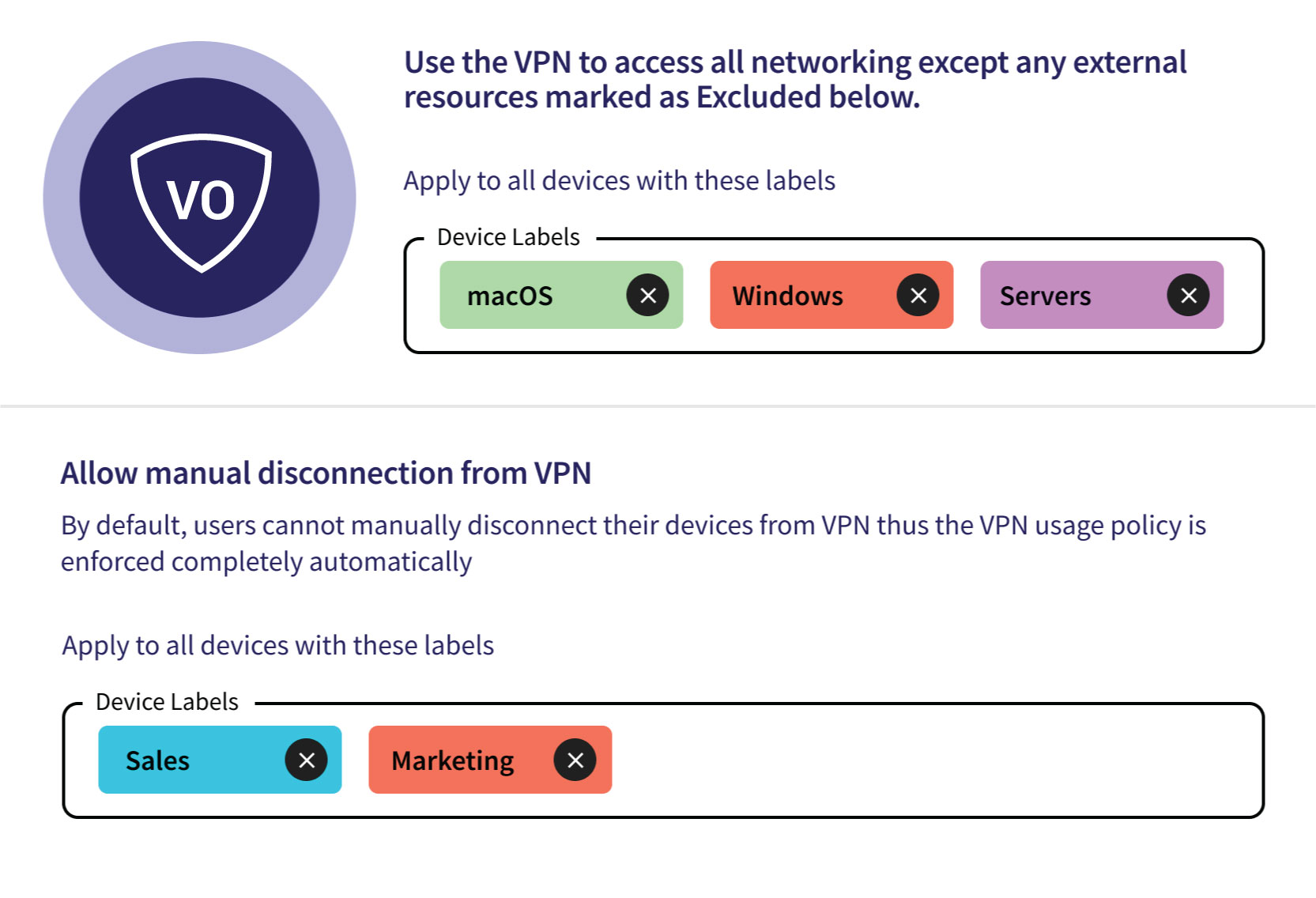
Network
Network Security is one of the core SASE modules in Keplersafe. Capabilities in this module include:
- Remote Office Cluster: Protect your corporate network against hijacking, intrusion, adware, malware, and phishing attacks.
- Cloud VPN: Encrypt all network data for remote users without hurting performance or increasing management overhead.
- Cloud Firewall: Route all traffic through a virtual, cloud firewall, stripping out malicious before they can attack your devices.
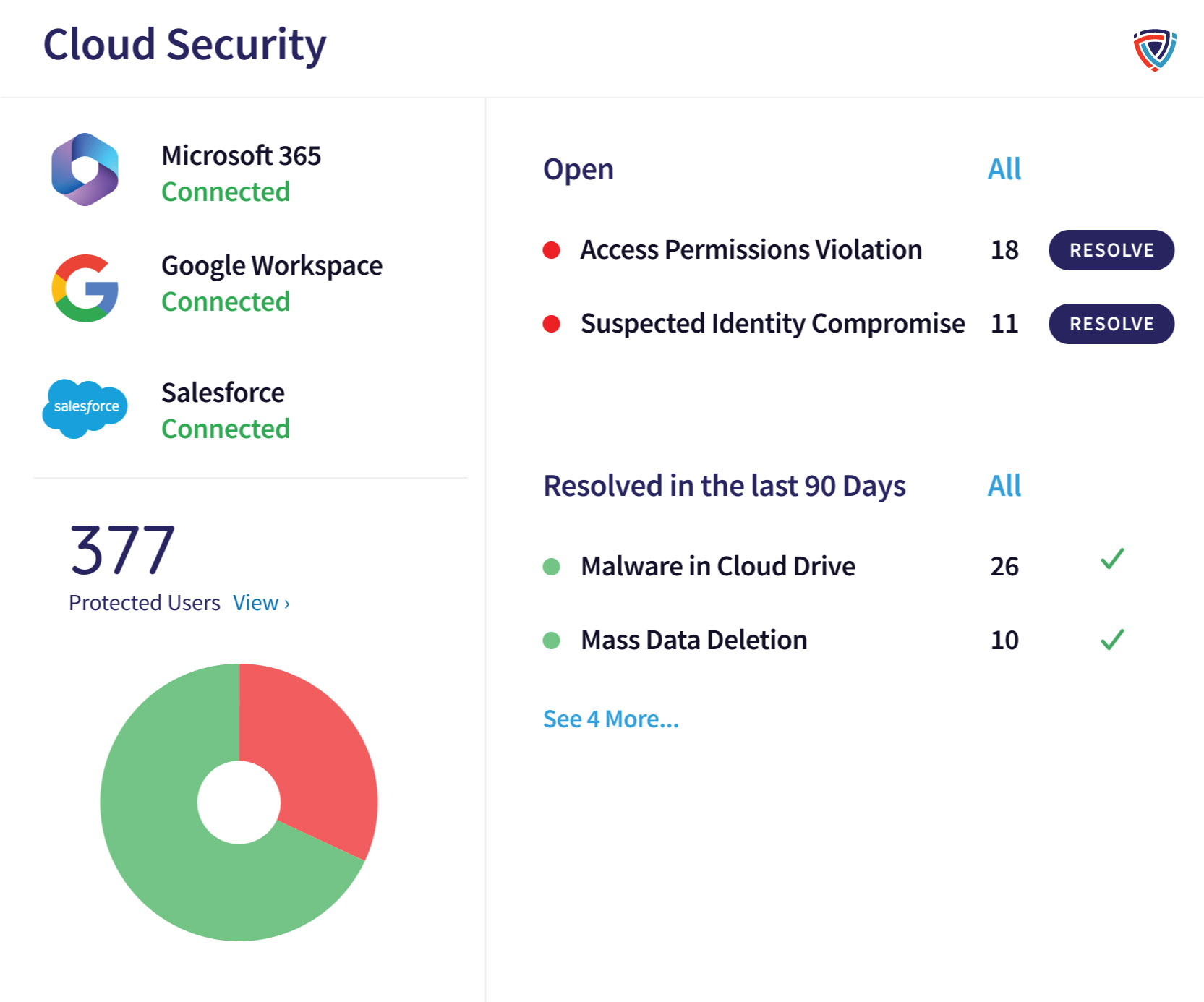
Cloud Security
Cloud Security is one of the core SASE modules in Keplersafe.
With it, you can stop abnormal admin activity, access violations, ID compromise, malware, and mass data changes in the following cloud apps: Microsoft Office 365, Google Workspace, Slack, Dropbox, Box, and Salesforce.
Blocks:
- Abnormal admin activity
- Malware in cloud drive
- Suspected identity compromise
- Access permissions violation
- Suspected bot attacks
- Mass download
- Mass deletion
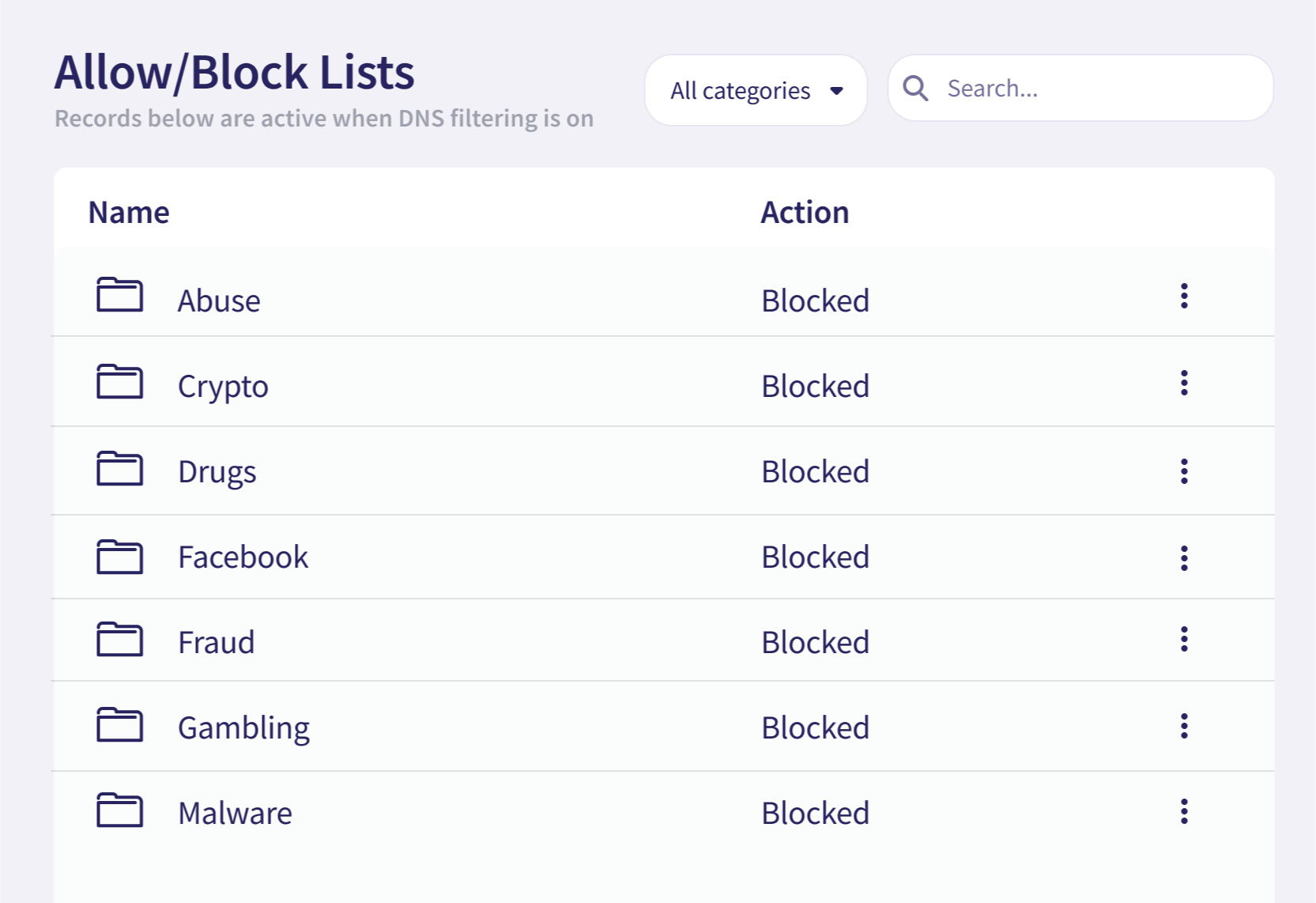
Secure Web Gateway
The Secure Web Gateway (SWG) add-on lets you apply DNS filtering to restrict network traffic. DNS filtering can protect your business from malware, viruses, and other potential threats.
Capabilities:
- DNS Filtering: Block access to undesired external resources from your virtual office.
- Allow/Block Lists: Restrict access to specific URLs, groups of URLs, or content categories.
Zero Trust Network Access
The Zero Trust Network Access module (ZTNA) lets you apply strict security protocols for remote workers without hindering end-user productivity.
To guard and protect remote work, you can verify each user, device, and network flow before granting access to corporate resources.
