The Keplersafe Platform
Meet Modular Cybersecurity
One dashboard.
One endpoint agent.
One data engine.
And 14 security modules that snap into place.
This is how Keplersafe is changing cybersecurity.

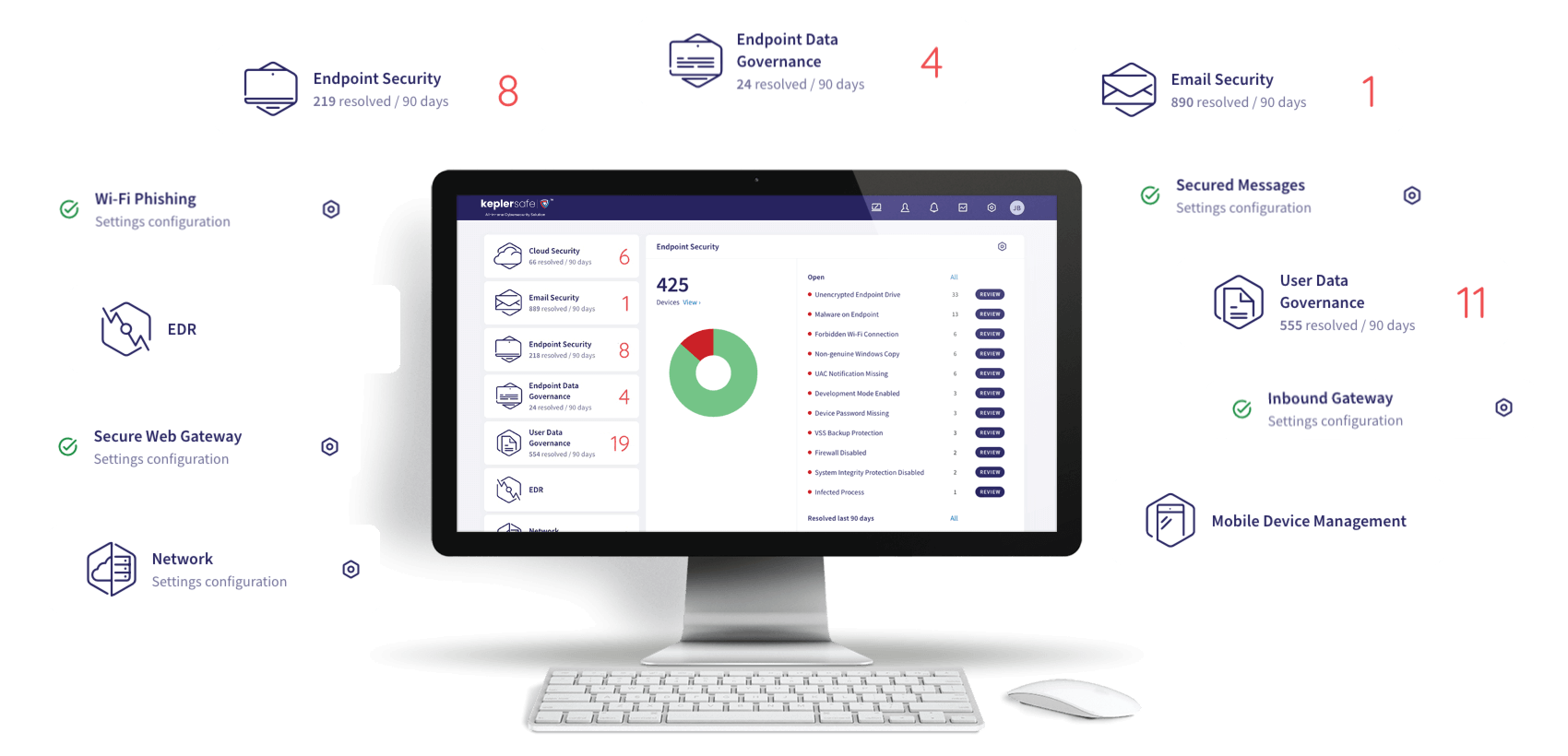
One Dashboard for Everything
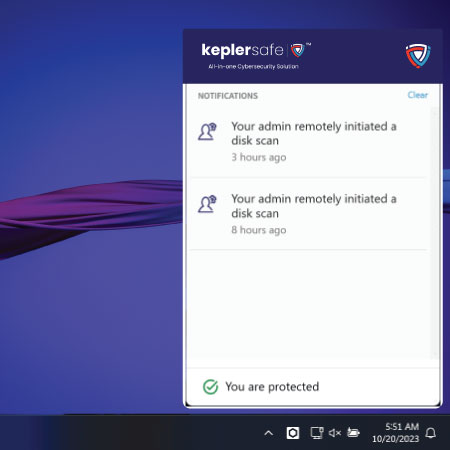
One Endpoint Agent for All Modules
Keplersafe works across Windows, Windows Server, and Mac OS.
A Growing Collection of Security Modules
Access Management
Ensure secure access to resources by managing user identities and access privileges.
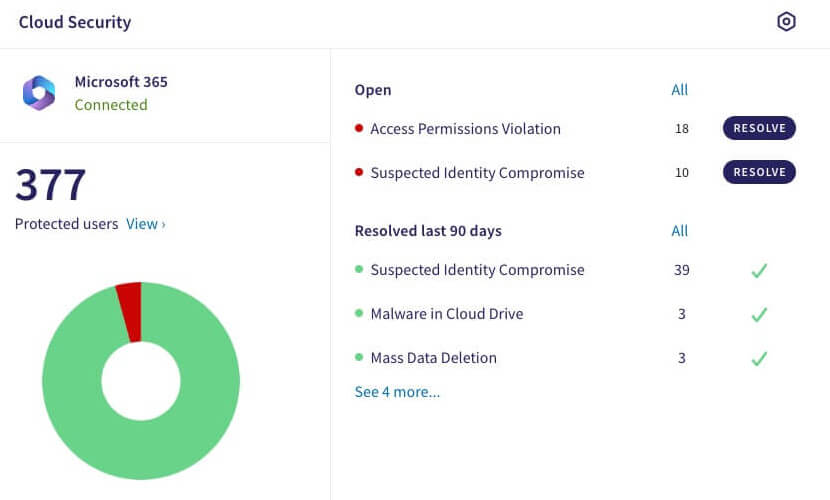
Cloud Security
Protect assets hosted on platforms like AWS and Azure and cloud access security broker (CASB).
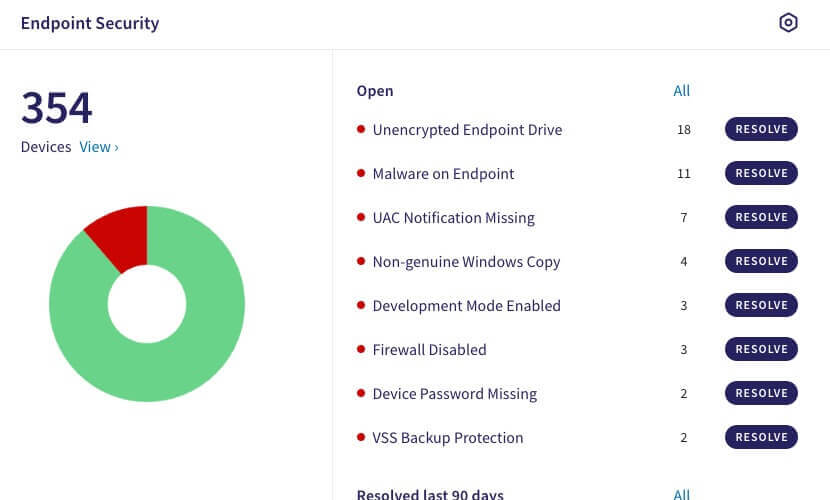
Endpoint Security
Protecting individual devices (endpoints), encompassing antivirus and anti-malware solutions.
Incident Response
Help organizations prepare for, respond to, and recover from cybersecurity incidents.
Managed Security
Encompass outsourcing various security functions to third-party providers.
Mobile Device Security
Focus on securing mobile devices and applications used within an organization.
Access Management
Ensure secure access to resources by managing user identities and access privileges.
Cloud Security
Protect assets hosted on platforms like AWS and Azure and cloud access security broker (CASB).
Endpoint Security
Protecting individual devices (endpoints), encompassing antivirus and anti-malware solutions.
Incident Response
Help organizations prepare for, respond to, and recover from cybersecurity incidents.
Managed Security
Encompass outsourcing various security functions to third-party providers.
Mobile Device Security
Focus on securing mobile devices and applications used within an organization.
Network Security
Focus on safeguarding an organization's network infrastructure from cyber threats.
Risk Management
Managing cybersecurity risks and complying with industry regulations and standards.
Security Awareness
Educate employees about cybersecurity best practices and risks in recognizing threats.
Security Consulting
Expert guidance to organizations in creating robust cybersecurity strategies.
Security Information
Collecting and analyzing data from various sources to provide real-time threat monitoring.
Vulnerability Assessment
Vulnerability scanning assesses system works, while penetration testing involves ethical hacking.
Network Security
Focus on safeguarding an organization's network infrastructure from cyber threats.
Risk Management
Managing cybersecurity risks and complying with industry regulations and standards.
Security Awareness
Educate employees about cybersecurity best practices and risks in recognizing threats.
Security Consulting
Expert guidance to organizations in creating robust cybersecurity strategies.
Security Information
Collecting and analyzing data from various sources to provide real-time threat monitoring.
Vulnerability Assessment
Vulnerability scanning assesses system vulnerabilities, while penetration testing involves ethical hacking to test an organization's defenses.
We Can Manage Cybersecurity for You
We've Created Suites that Cover Your Security Needs in Each Domain
Keplersafe Essentials
Get essential coverage for endpoints, email, and cloud apps, automating resolution of most security incidents.
- Endpoint Security
- Endpoint Detection & Response (EDR)
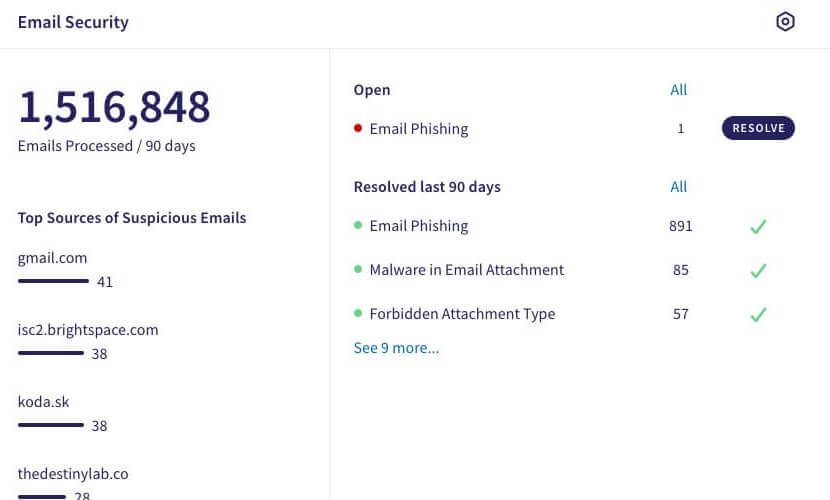
- Email Security
- Cloud Security
Endpoint Protection
- Endpoint Security
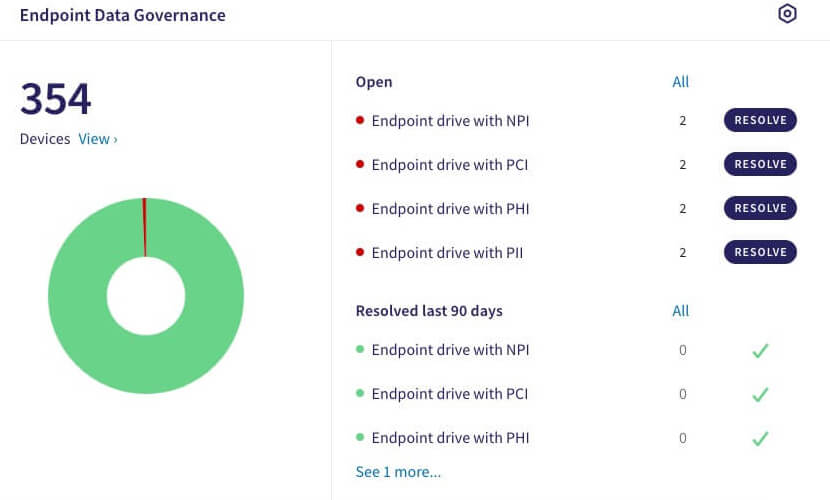
- Endpoint Data Governance
- Endpoint Detection & Response (EDR)
- Wifi Phishing
- Add Managed Endpoint Security
Email Protection
- Endpoint Security
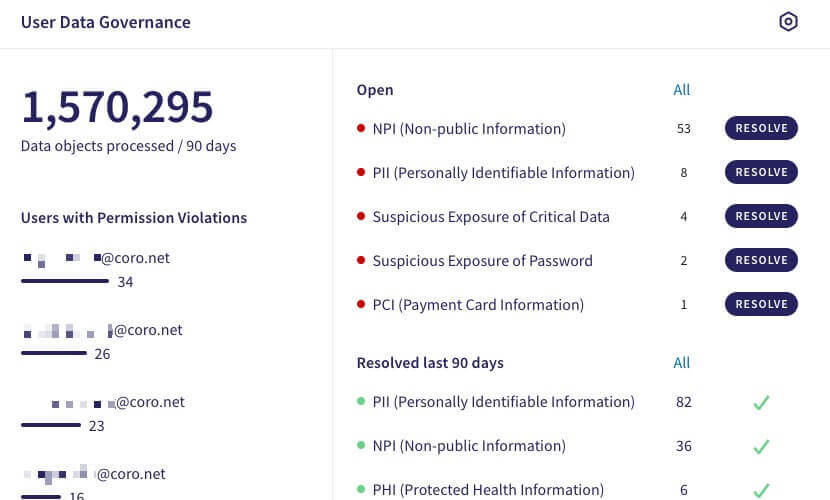
- User Data Governance
- Secure Messaging Encryption
- Inbound Gateway
- Add Managed Email Security
Secure Access Service Edge (SASE)
- Network Security
- Cloud Security
- Secured Web Gateway
- Zero Trust Network Access (ZTNA)
- Add Managed Network & Cloud Security
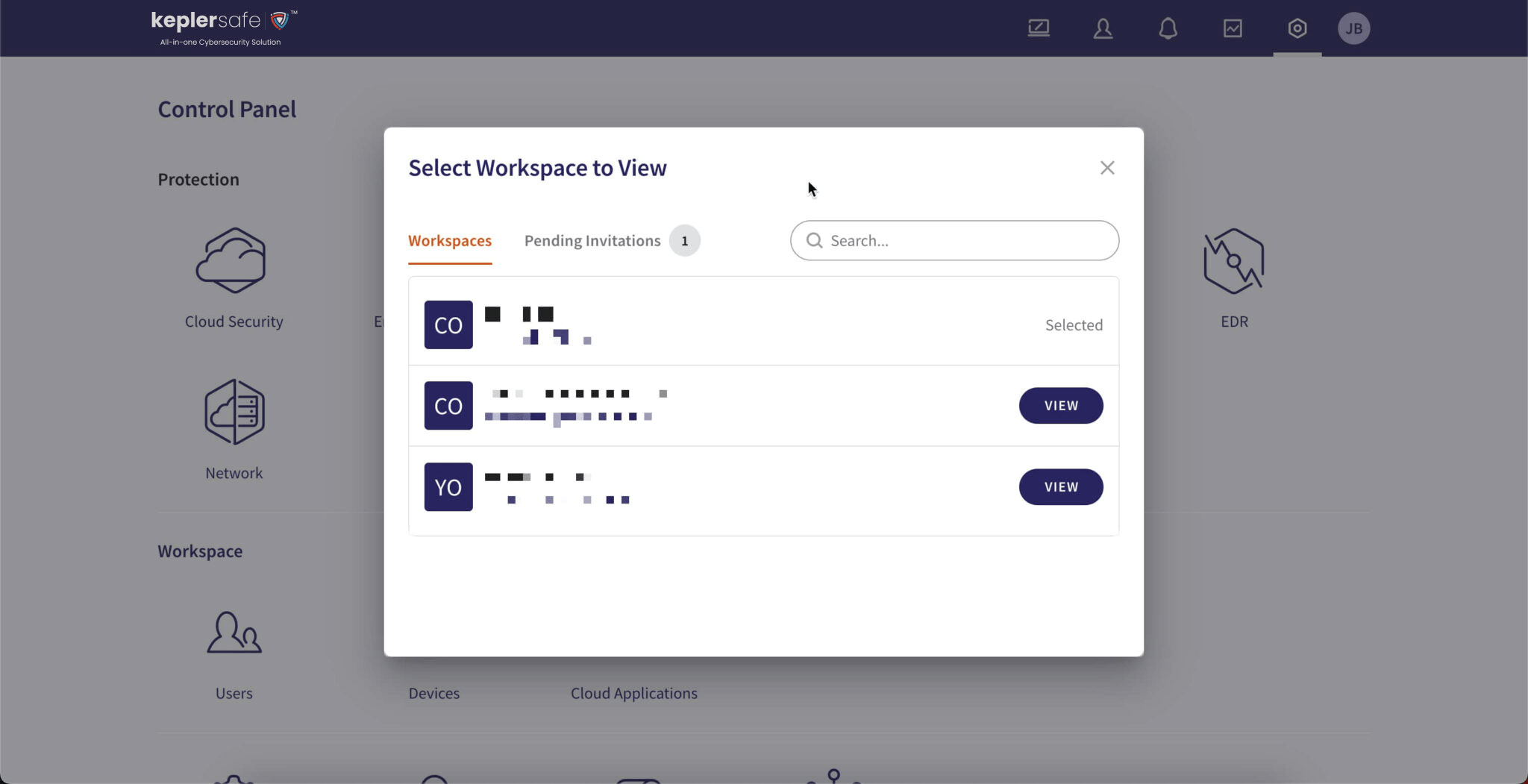
Centrally Manage Multiple
Instances of Keplersafe
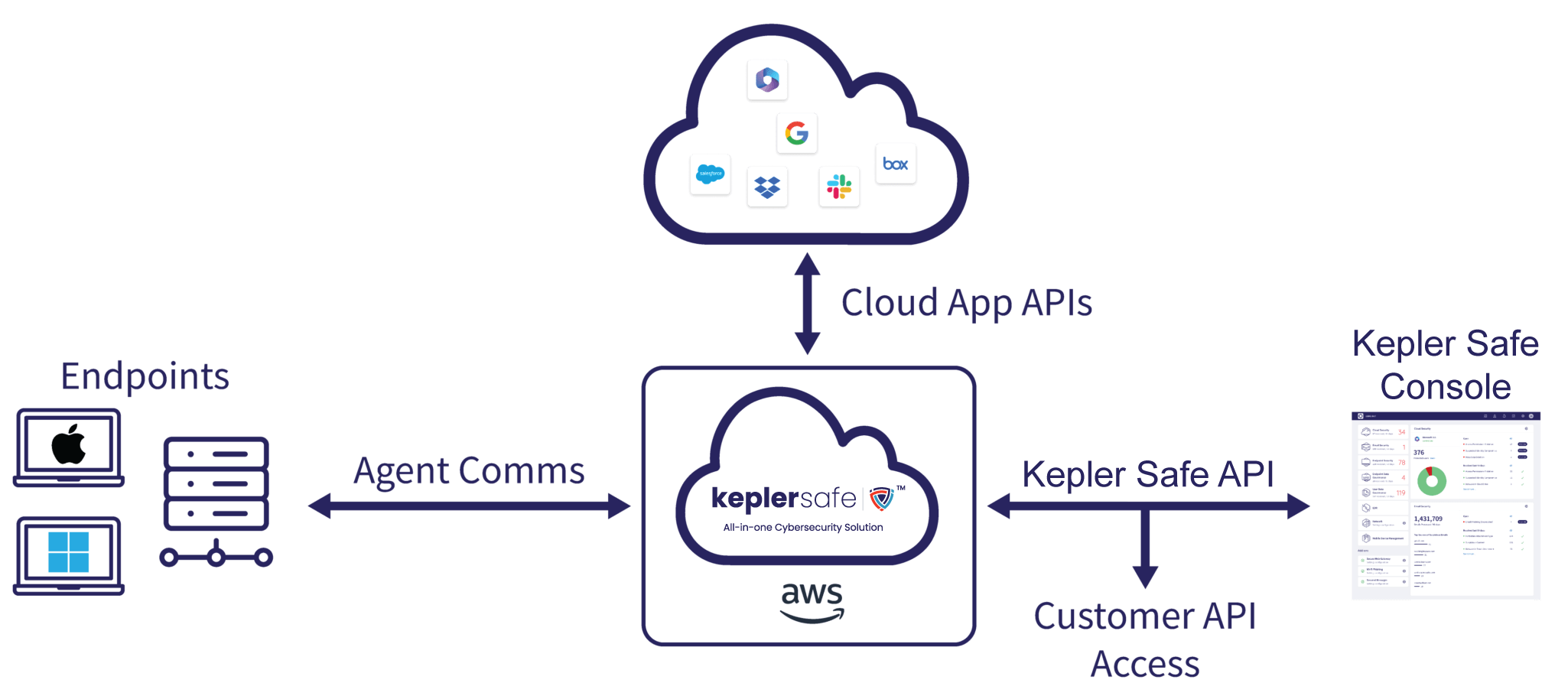
How Keplersafe Works
IT Director - Mid-Market G2Crowd Review
I'm so glad I did choose Kepler Safe for cyber security! Their team was incredibly knowledgeable and professional, and they took the time to explain everything to me in a language I could understand.
Seth B
Kepler Safe users since 2020
Overall, my experience with Kepler Safe has been positive, and I would recommend their services to anyone looking for a reliable cyber security solution.
IT Director - Mid-Market G2Crowd Review
I'm so glad I did choose Kepler Safe for cyber security! Their team was incredibly knowledgeable and professional, and they took the time to explain everything to me in a language I could understand.
Seth B
Kepler Safe users since 2020
Overall, my experience with Kepler Safe has been positive, and I would recommend their services to anyone looking for a reliable cyber security solution.
Peace of Mind is Within Your Reach
and vulnerabilities for your entire business.
