Forging A Cyber-Security Haven for The Government!
Software technology companies are the favorite target of cyber attacks.
#1
Ransomware is the the #1 attack vector against technology companies
80%
of breaches involve system intrusion, errors, and basic web application attacks
$3.33M
average cost of human errors in cybersecurity breaches
Securing Government IT Infrastructure Beyond the Digital Horizon!
All-In-One Cyber Security Services for The Government Sector!
With Kepler Safe’s comprehensive suite of services, government organizations can confidently navigate the digital horizon, knowing that their IT infrastructure is fortified against cyber threats. We are committed to securing your systems, protecting sensitive data, and ensuring the continuity of critical government operations in an increasingly interconnected world.

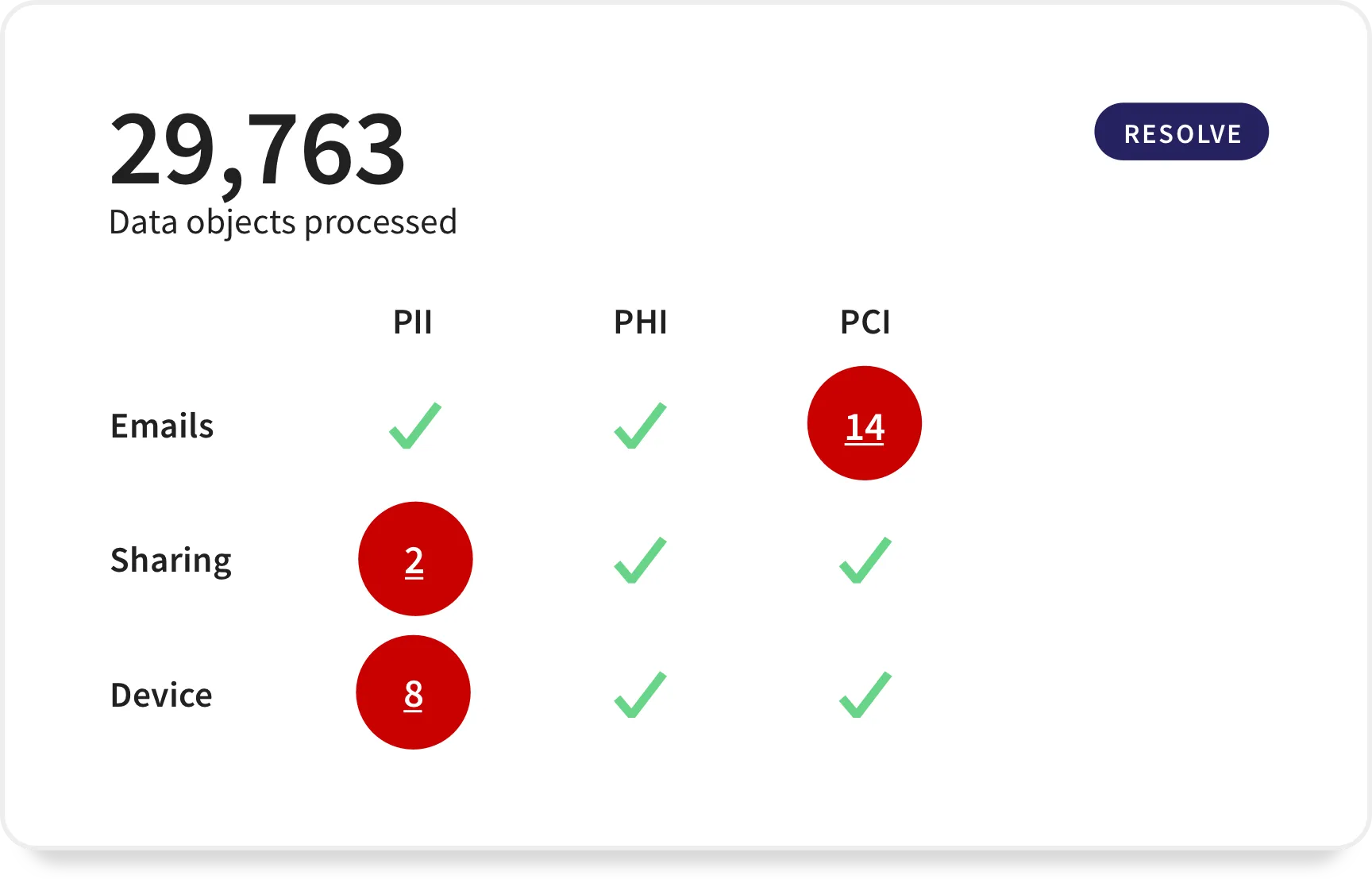
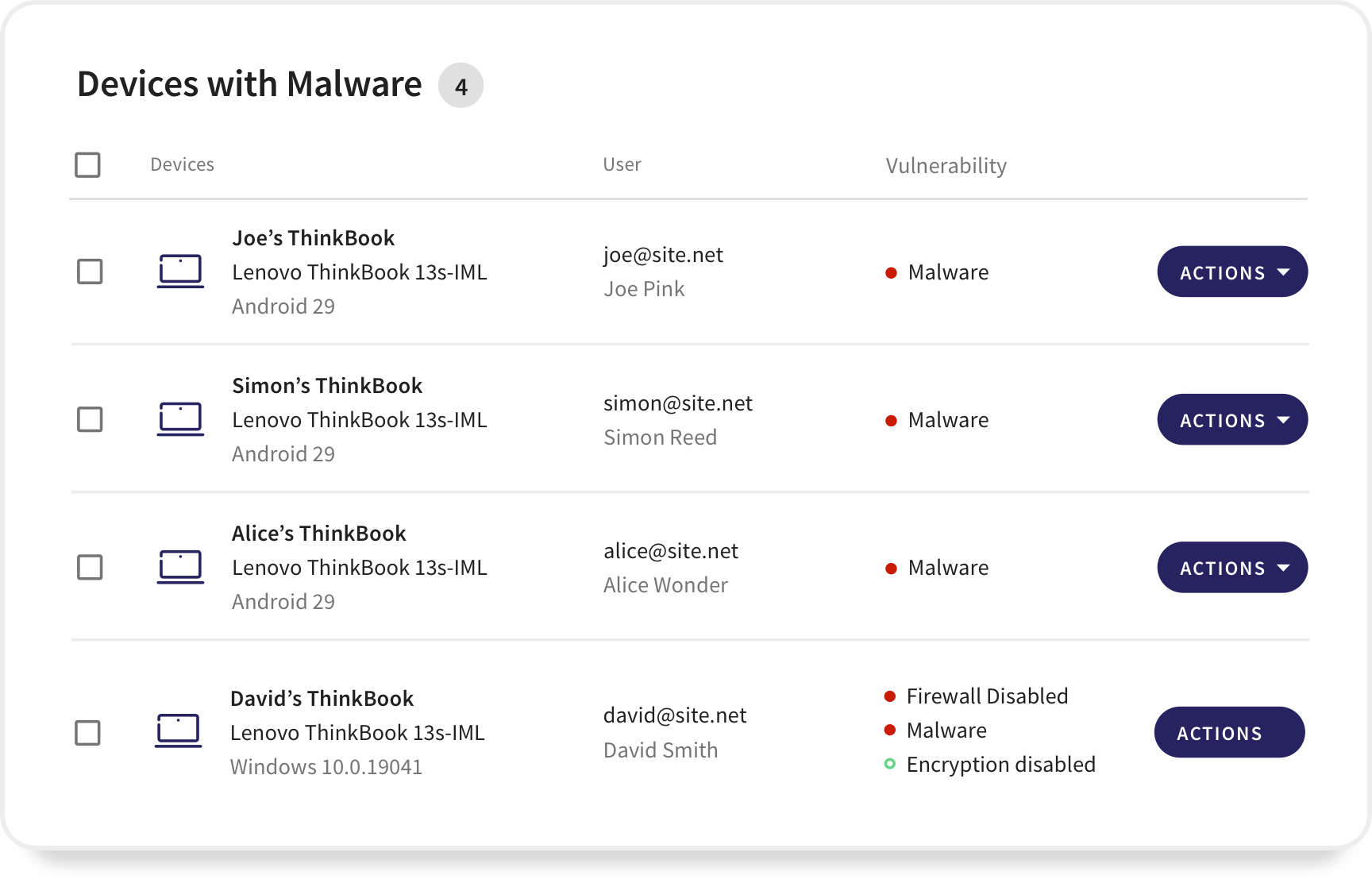
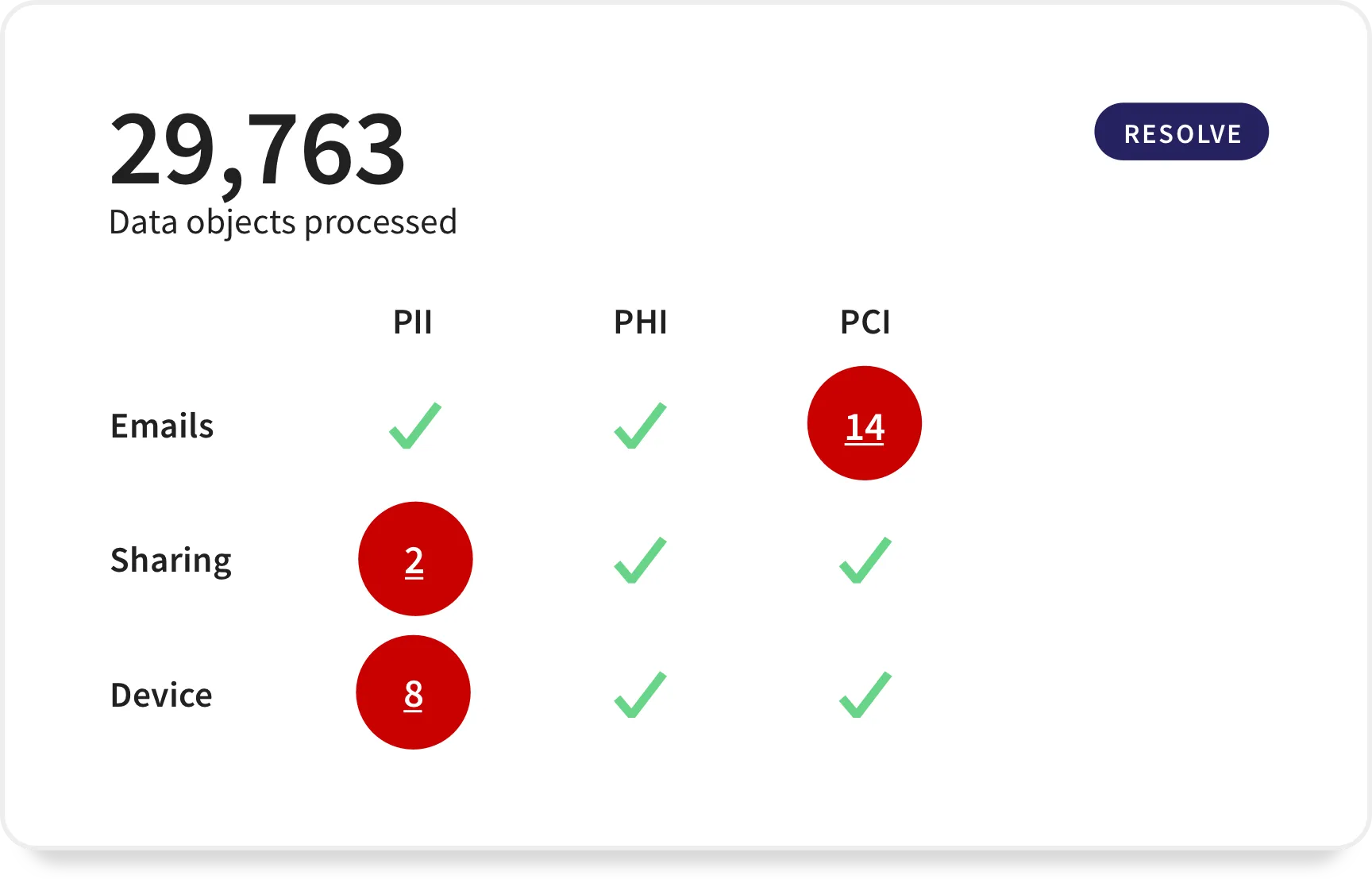
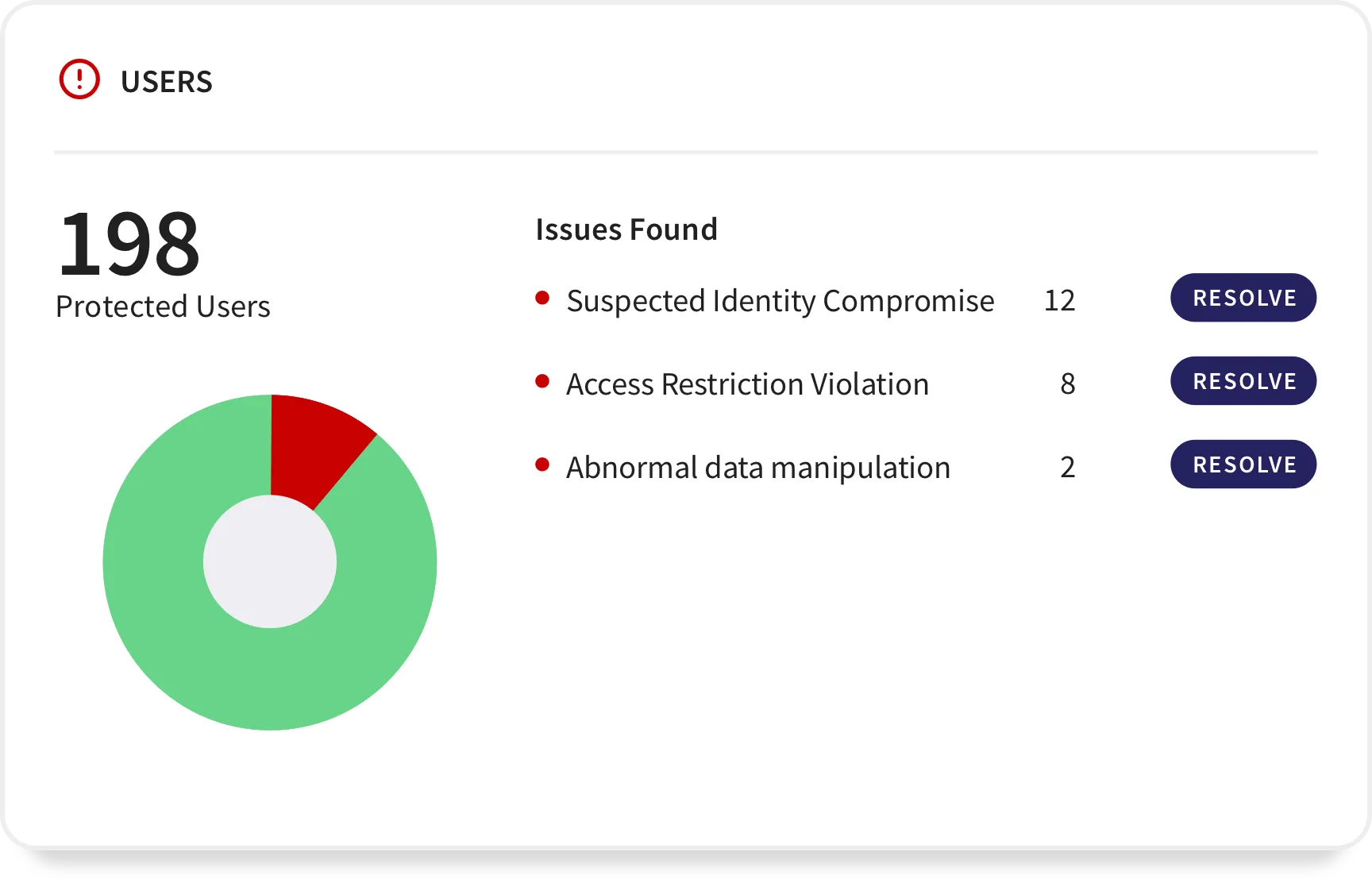
Our cutting-edge technologies and proactive monitoring systems enable us to detect and thwart advanced cyber threats before they can penetrate government networks. From identifying sophisticated malware to uncovering insider threats, we leave no stone unturned in protecting your IT infrastructure.
We deploy state-of-the-art firewalls, intrusion detection and prevention systems, and secure network architecture to fortify your government networks. Our team of cyber security experts designs and implements tailored security solutions that defend against unauthorized access, data breaches, and network vulnerabilities.
Our skilled cybersecurity professionals conduct comprehensive vulnerability assessments and penetration tests to identify weaknesses in your IT infrastructure. By simulating real-world attack scenarios, we help you proactively address vulnerabilities, reinforce security measures, and bolster the resilience of your systems.
In the event of a cyber incident, our rapid incident response team is ready to mitigate the impact and minimize downtime. We employ industry best practices and cutting-edge cyber security techniques to investigate and identify the source of the breach, ensuring that necessary actions are taken promptly to restore normalcy.
We believe that cybersecurity is a shared responsibility. Through engaging and interactive training programs, we empower your government employees with the knowledge and skills to recognize and respond to cyber threats effectively. By fostering a culture of security awareness, we strengthen the human firewall against social engineering attacks.
With 24/7 monitoring and real-time threat intelligence, we provide continuous visibility into the security posture of government IT infrastructure. By leveraging advanced security information and event management (SIEM) tools, we detect anomalies, identify potential threats, and take proactive measures to safeguard critical systems.
Why Do Government Organizations Need Cybersecurity Services?
National Security
Public Perception and Accountability
Compliance and Regulatory Requirements
Insider Threats
Providing The Government with A Quantum Leap into Cyber Security!
Kepler Safe brings cutting-edge cyber defense to software technology companies.






Playing The Part in The Government’s Epic Quest for Cyber Security!
Expertise and Experience
Kepler Safe brings a wealth of expertise and experience who stay at the forefront of industry trends, constantly expanding their knowledge to tackle the latest threats.
Comprehensive Solutions
We offer a comprehensive suite of cyber security services that cover every aspect of your organization's digital defenses. We are your one-stop shop for all your cyber security requirements.
Cutting-Edge Technologies
Our solutions harness the power of artificial intelligence, machine learning, and quantum-inspired algorithms to detect, prevent, and mitigate cyber threats with exceptional accuracy and speed.
Proactive Threat Intelligence
We continuously monitor the cyber security landscape, allowing you to implement preemptive measures and ensure that your organization is prepared to counter potential threats.
Compliance and Regulatory Support
Kepler Safe has in-depth knowledge of frameworks and can guide you through the complexities of compliance, ensuring that your cyber security practices align with industry standards.
Customer-Centric Approach
At Kepler Safe, we take the time to understand your specific cyber security needs, challenges, and goals, tailoring our services to meet your requirements effectively.
Don't go at it alone. Let Kepler Safe
support you.
Connect your business to Kepler Safe with a click. Enjoy immediate detection of threats and
vulnerabilities for your entire business free forever.
