Simplified cybersecurity for educational institutions
What we do

How we do it
Our intuitive platform takes just moments to install and can secure your entire institution. Keplersafe combines the agility of an API-based platform with the scrutiny and ingenuity of artificial intelligence/machine learning.
Customizable
Configure the platform and automations based on your business needs and policies
Around-the-clock monitoring
Keplersafe monitors your environments 24/7/365, identifying and immediately mitigating threats
Endpoint protection
Continuous scanning and remediation for malware on all your devices (endpoints), cloud applications, and email accounts
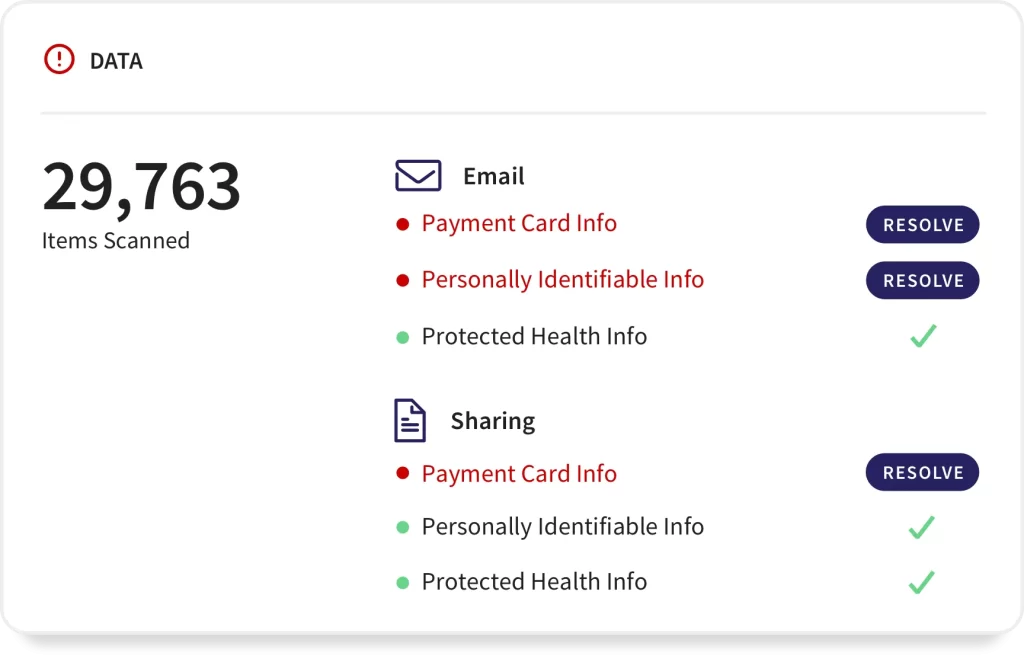
Data governance protection
Automatically scans files and emails across all devices for regulatory data such as PII/PCI/PHI information, recognizing and alerting on potential leaks
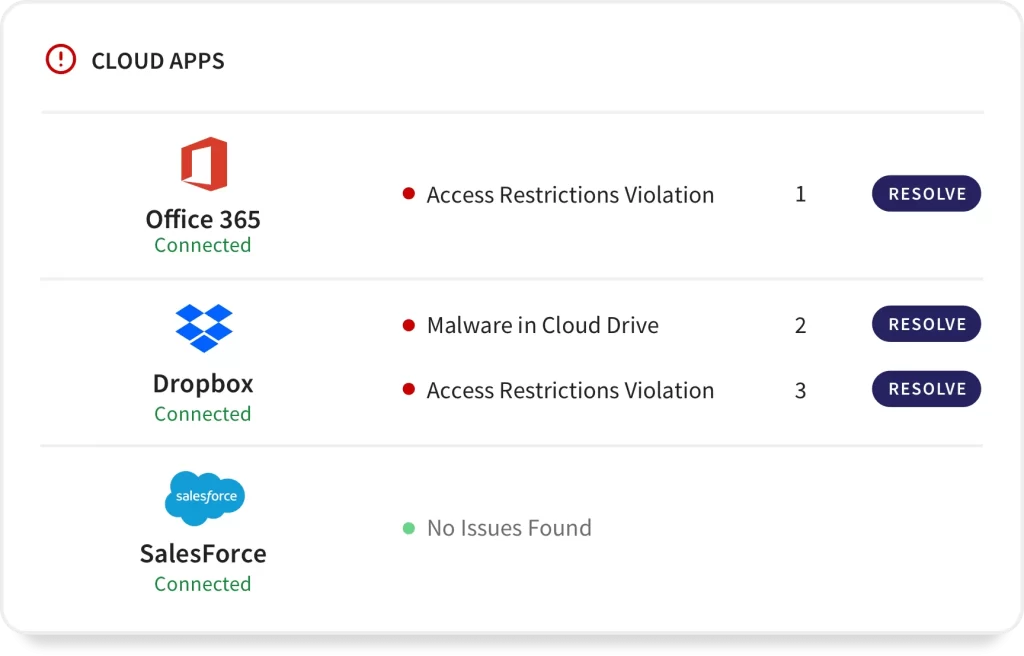
Access control protection
Protects against bad actors and internal threats by recognizing abnormal login patterns, blocking hacking attempts automatically, and more
Automatic mitigation
Keplersafe recognizes threats and quarantines them immediately, sharing the information with you and enabling you to investigate manually if you want
Why Do educational institutions Need Cybersecurity Services?
Protect your most-sensitive data
Keplersafe is the central control point for sensitive data and user activity, enabling you to enforce a wide range of security, regulatory, and company policies.
- Ensure compliance
- Prevent unauthorized data sharing or access
- Automatically identify regulatory violations
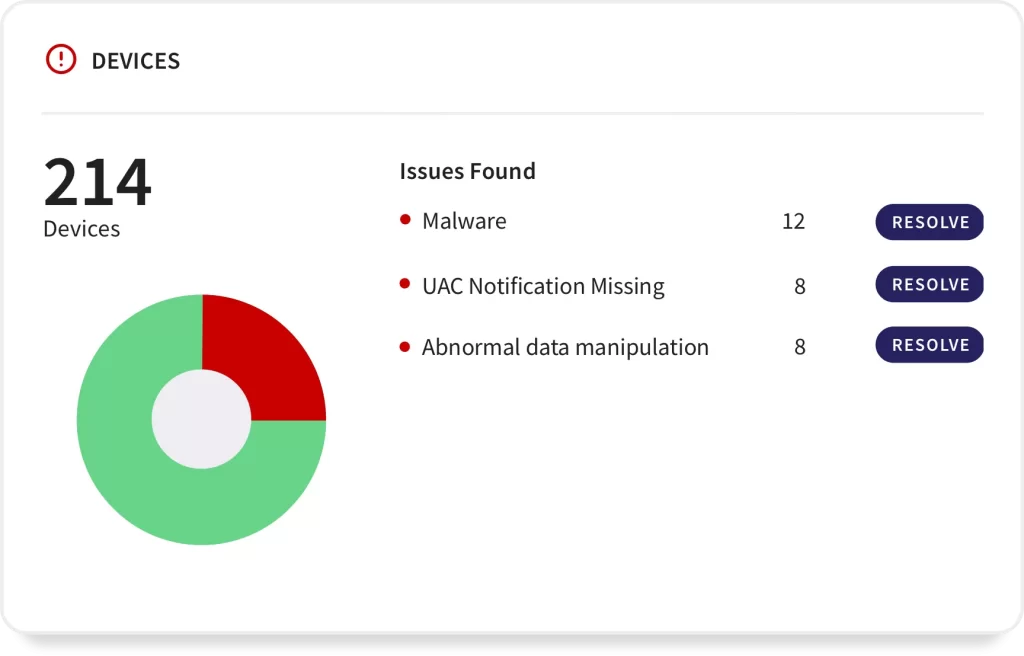
Identify potential ransomware and malware
Keplersafe AI-powered approach automatically distinguishes between human and bot-generated actions. You can detect potential attacks and automatically remediate them by suspending suspect users and preventing further corruption of files.
Block phishing scams, ransomware, and malware instantly
Suspicious email activity is automatically detected and blocked
Prevent unauthorized data sharing
Manage sharing at the file, folder, and user levels with collaboration rules that assign specific permissions, including whitelists of external collaborators.
Automatically limit the scope of sharing permissions and revoke shared links to protect data and files.
Unauthorized account activities: Know when an account has been compromised or when an insider or privileged user is acting like a threat.