One platform that includes all you need to secure your business

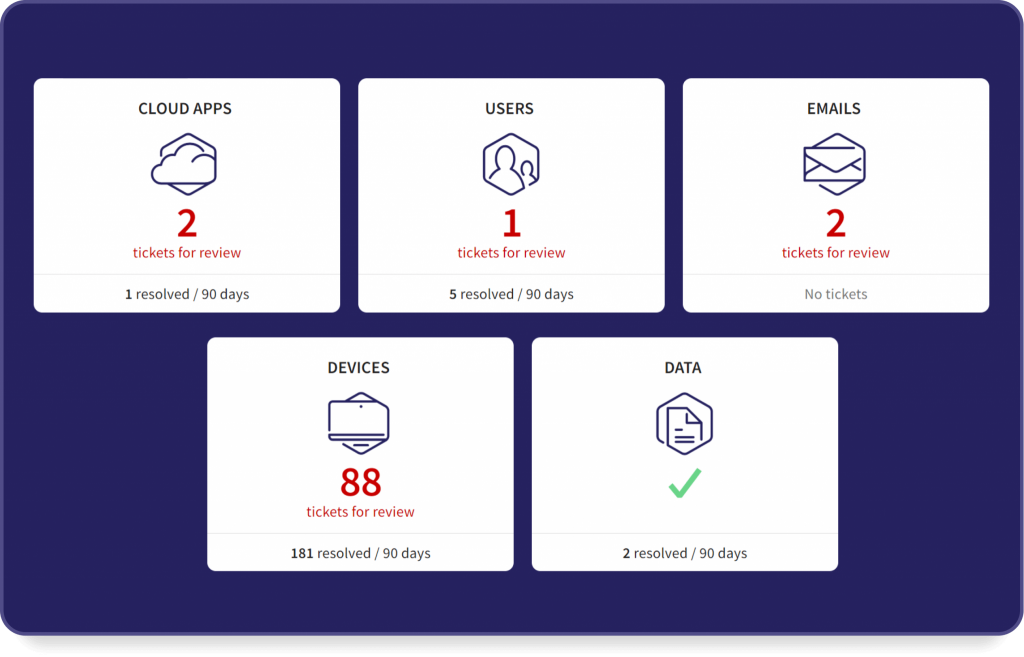
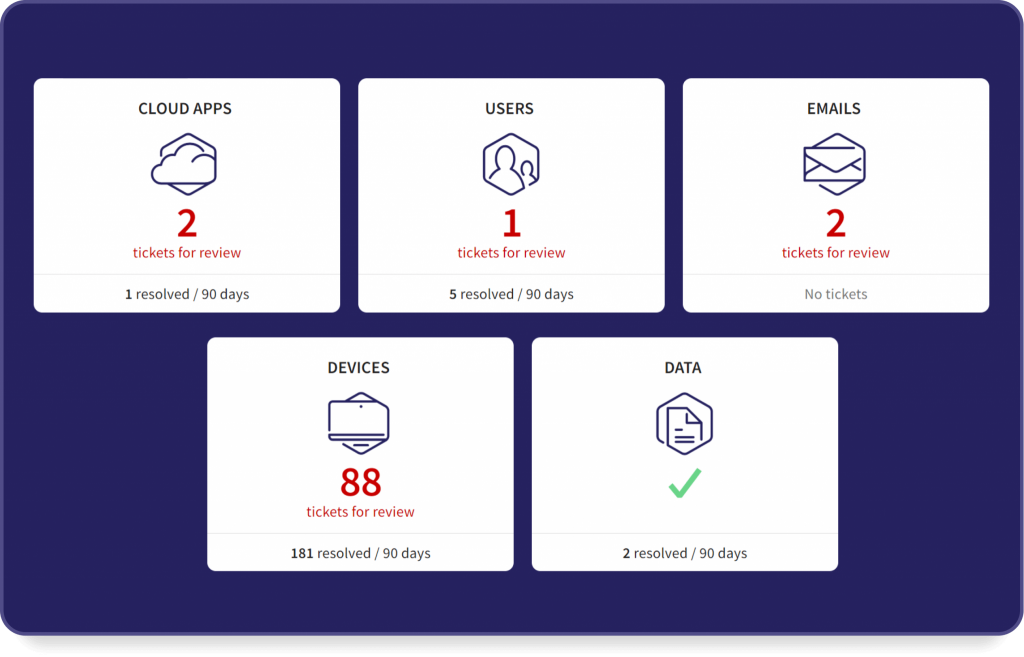
Cloud Apps

Users

Endpoint Devices

Data
Simple, modern, unified approach to cybersecurity
See how Kepler Safe makes your life a lot easier
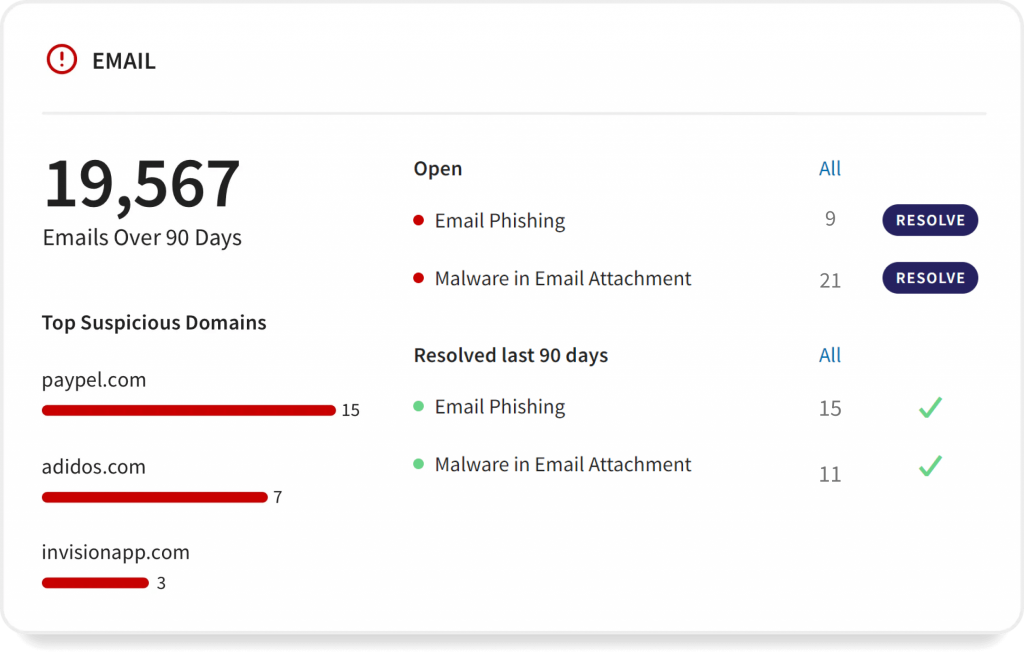
Email Protection
Kepler Safe's vigilant AI technology monitors your email to keep an eye out for unusual behavior.
If we see a suspicious email or an email coming from a flagged IP address, we isolate the threat immediately.
This gives you the opportunity to detect the threats facing your company and remediate as necessary.
Cloud Apps Protection
- Connect cloud apps for continuous protection, in minutes.
- Implement collaboration rules that assign specific permissions, including whitelists of external collaborators
- Get automatic identification of regulatory violations for HIPAA and GDPR. We also help meet GLBA, CCPA, SOC 2, and SOX compliance standards.
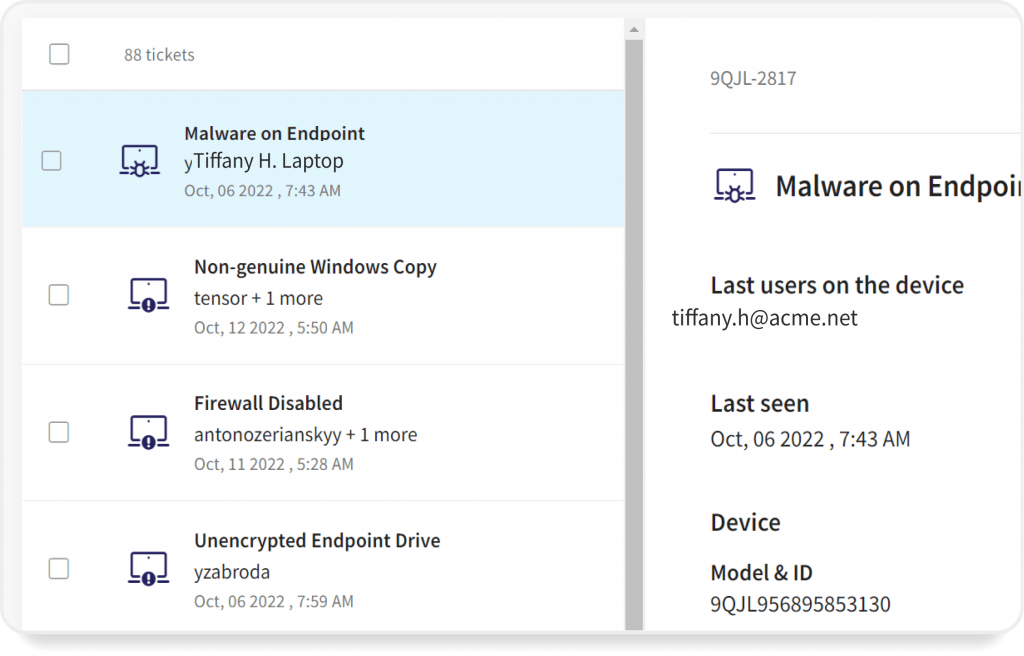
Endpoint Protection
- Allow only authorized appliances to access your systems
- Manage and monitor devices in real-time around the clock
- Prevent malware, ransomware, and phishing from being uploaded from devices into your environment
- Configure automatic remediation for detected threats (malicious software, files, processes, etc.)
Data Protection
Get automatic identification of regulatory violations for HIPAA and GDPR. We also help with meeting compliance standards for GLBA, CCPA, SOC 2, and SOX.
Everybody talks about DLP, but data leakage is just a part of the problem. Full data protection must cover the identity of the user and devices accessing the platform, device security postures, and networks being used, both in-house and in the wild.