ALL-IN-ONE CYBER SECURITY SOLUTIONS
Modular Cybersecurity
14 Enterprise-grade Modules, One Platform
We use a strong defense mechanism to keep your users, devices, email, cloud apps, and data protected!
Access Management
Ensure secure access to resources by managing user identities and access privileges.
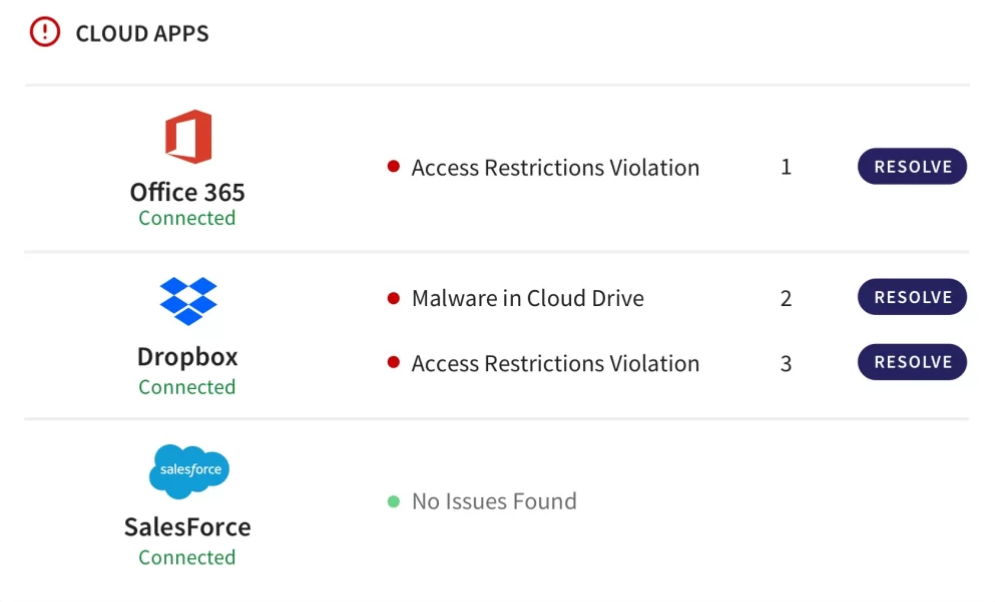
Cloud Security
Protect assets hosted on platforms like AWS and Azure and cloud access security broker (CASB).
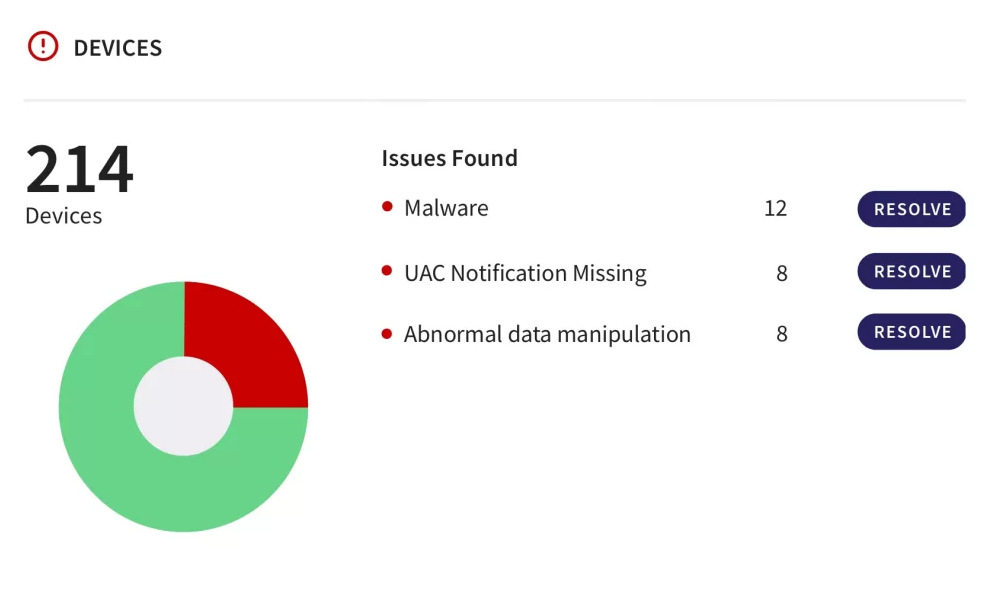
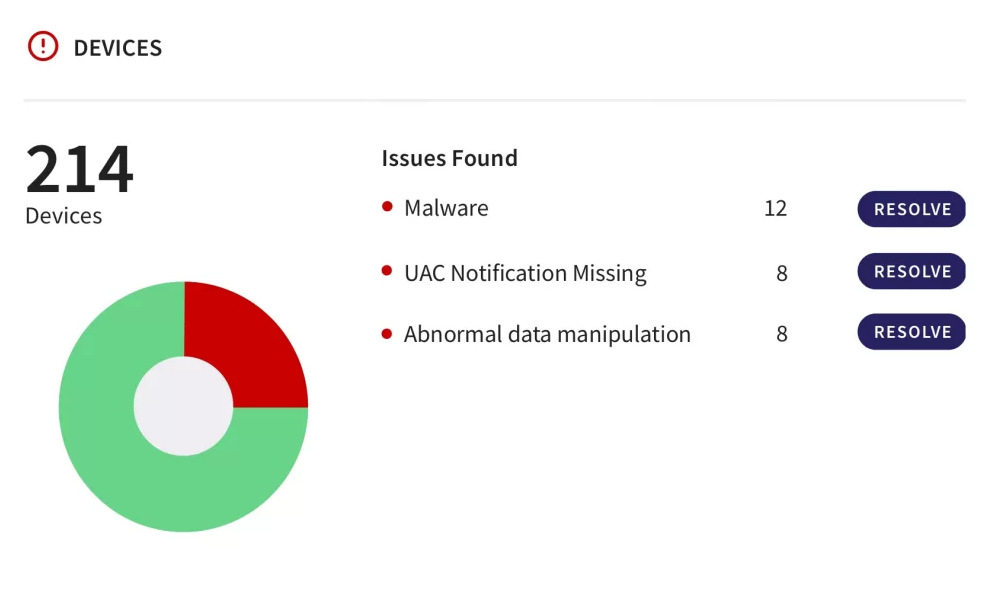
Endpoint Security
Protecting individual devices (endpoints), encompassing antivirus and anti-malware solutions.
Incident Response
Help organizations prepare for, respond to, and recover from cybersecurity incidents.
Managed Security
Encompass outsourcing various security functions to third-party providers.
Mobile Device Security
Focus on securing mobile devices and applications used within an organization.
Access Management
Ensure secure access to resources by managing user identities and access privileges.
Cloud Security
Protect assets hosted on platforms like AWS and Azure and cloud access security broker (CASB).
Endpoint Security
Protecting individual devices (endpoints), encompassing antivirus and anti-malware solutions.
Incident Response
Help organizations prepare for, respond to, and recover from cybersecurity incidents.
Managed Security
Encompass outsourcing various security functions to third-party providers.
Mobile Device Security
Focus on securing mobile devices and applications used within an organization.
Network Security
Focus on safeguarding an organization's network infrastructure from cyber threats.
Risk Management
Managing cybersecurity risks and complying with industry regulations and standards.
Security Awareness
Educate employees about cybersecurity best practices and risks in recognizing threats.
Security Consulting
Expert guidance to organizations in creating robust cybersecurity strategies.
Security Information
Collecting and analyzing data from various sources to provide real-time threat monitoring.
Vulnerability Assessment
Vulnerability scanning assesses system works, while penetration testing involves ethical hacking.
Network Security
Focus on safeguarding an organization's network infrastructure from cyber threats.
Risk Management
Managing cybersecurity risks and complying with industry regulations and standards.
Security Awareness
Educate employees about cybersecurity best practices and risks in recognizing threats.
Security Consulting
Expert guidance to organizations in creating robust cybersecurity strategies.
Security Information
Collecting and analyzing data from various sources to provide real-time threat monitoring.
Vulnerability Assessment
Vulnerability scanning assesses system vulnerabilities, while penetration testing involves ethical hacking to test an organization's defenses.
Featured Cyber Security Solutions for
Small and Medium Business

Setting the Standard In Cybersecurity - Here's What Sets Us Apart
| Kepler Safe | Others | |
|---|---|---|
| Budget | Cost Efficient | Expensive |
| Customer Support | 24/7 | Only on Weekdays (9 - 5) |
| Compliant | GDPR, HIPAA, and SOC 2 Compliant | Zero Compliances |
| Package | Single Solution | Different solution for Different Threats |
Recognized by Partners and Industry Leaders
Kepler Safe Understands Your Unique Industry Needs
Make Security Your Strong Suit with Kepler Safe!
Make Security Your Strong Suit with Kepler Safe!
Build a safe and compliant working environment for your users with our quick-to-install cyber security platform.
Stay Compliant with The Up to Date Security Regulations
The cyber threat intelligence mechanism that we use allows us to scan every file and email that passes through our network, identifying potential threats before they can cause harm.
Let Us Defend Your Inbox from Spam
Offering cutting-edge email security solutions where we use a vigilant AI technology that is specially designed to keep an eye out on your inbox for spam.
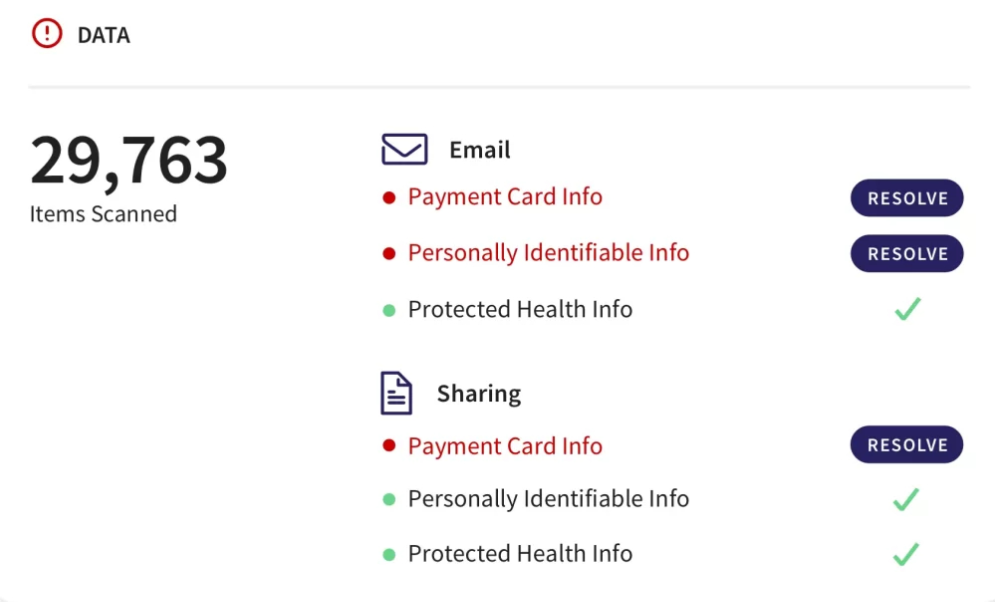
Keep Your Cloud Data Safe and Secure
Our cloud app protection takes the operational complexity and headaches out of cloud workload security, extending comprehensive protection to your public cloud assets.
Empowering You to Protect Your User Data
Protect the information of your users from insider threats, account hacking, and malicious activities by securing your endpoints with our symantec endpoint protection.
Pricing
Exclusive Low-Cost Cyber Security Package Just at $6/Month!
Starts at
$7
Monthly per module
FAQs About Kepler Safe and Its Capabilities
- Threat Intelligence
- Vulnerability Management
- Network Detection and Response (NDR)
- Endpoint Detection and Response (EDR)
- Behavioral Analytics
- Artificial Intelligence (AI)
- Conducting a risk assessment: Identifying potential threats and vulnerabilities in your technology platform, such as outdated software, unsecured networks, or weak passwords.
- Developing a cyber security plan: Create a plan that outlines the specific measures you will take to address these risks, such as implementing firewalls, antivirus software, and two-factor authentication.
- Integrating security into your platform: Implementing security controls into your technology platform, such as encryption, access controls, and intrusion detection systems.
- Training employees: Educate your employees on cybersecurity best practices, such as not clicking on suspicious links, using strong passwords, and reporting any security incidents.
- Regularly assessing and updating your security measures: Continuously monitoring your technology platform for potential threats and vulnerabilities, and making updates as necessary to keep your security measures up to date.
- Keep software up-to-date
- Use strong passwords
- Enable multi-factor authentication
- Use anti-virus and anti-malware software
- Educate employees
- Backup data regularly
WHAT THEY SAY ABOUT US
Testimonials
IT Director - Mid-Market G2Crowd Review
I'm so glad I did choose Kepler Safe for cyber security! Their team was incredibly knowledgeable and professional, and they took the time to explain everything to me in a language I could understand.
Seth B
Kepler Safe users since 2020
Overall, my experience with Kepler Safe has been positive, and I would recommend their services to anyone looking for a reliable cyber security solution.

Critical Flaw in ‘Windows Hello’ Authentication: What It Means for Users
The consumer electronics giant disclosed its findings on a cyberattack in March, which involved data exfiltration impacting its Japanese operations.... read more

Fujitsu Suffers Worm-Like Attack From Something That Wasn’t Ransomware
The consumer electronics giant disclosed its findings on a cyberattack in March, which involved data exfiltration impacting its Japanese operations.... read more

Intel CPUs Vulnerable to Spectre-Like ‘Indirector’ Attack, Compromising Data Security
Researchers from the University of California San Diego (UCSD) have discovered a novel method to launch Spectre-like side-channel attacks on... read more

Effective Cybersecurity MSP Tactics to Prevent Cyber Attacks
In today’s digital era, cyberattacks have become increasingly sophisticated and prevalent, posing significant risks to businesses of all sizes. read more

WordPress Plugins Hit by Widespread Supply Chain Attack
A threat actor, or possibly multiple actors, has breached several plugins on the WordPress.org platform. These plugins have been compromised... read more

UwU Lend Faces a New $3.7 Million Hack Amid Ongoing Reimbursement Efforts
In a concerning turn of events, the UwU Lend protocol, which suffered a nearly $20 million hack on June 10,... read more

ZeroLogon Vuln Targeted by RansomHub Actors in Recent Ransomware Attack
In the latest series of attacks by the rapidly expanding RansomHub ransomware, cybercriminals have taken advantage of the critical ZeroLogon... read more

Hackers target Check Point Software customers through old, local VPN accounts
Check Point Software Technologies has alerted its customers that malicious actors are attempting to hack a limited number of old... read more
