ALL-IN-ONE CYBER SECURITY SOLUTIONS
Modular Cybersecurity
14 Enterprise-grade Modules, One Platform
Keplersafe cybersecurity modules snap together with a click of a button. No integration, no headaches. One pane of glass, one endpoint agent, one AI-driven data engine. One security platform with all the modules you need.
What Makes Keplersafe Different?
training employees on each one, and dealing with multiple interfaces and endpoint agents. Until now. Keplersafe is one platform with many modules.
Get all the security you need now, with the ability to switch on any module you need in the future.
One
Interface
One
Endpoint Agent
One
Data Engine
Security Modules that Snap into Place
Some enhance other modules. Each KeplerSafe module has won awards in its security domain, outperforming many market leading point solutions.*
Inbound Gateway
Intercept inbound emails so only safe senders reach recipients.
Wifi Phishing
Prevent end users from connecting to suspicious wifi endpoints.
Secure Web Gateway
Filter web traffic to protect your business from malicious apps and sites.
Secure Message Encryption
Encrypt outbound emails so only recipients can view.
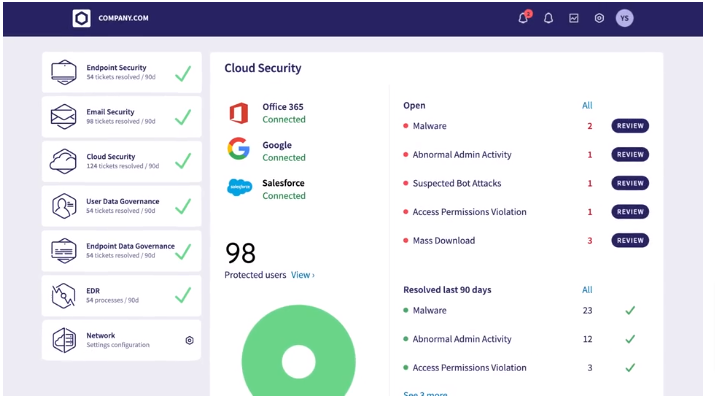
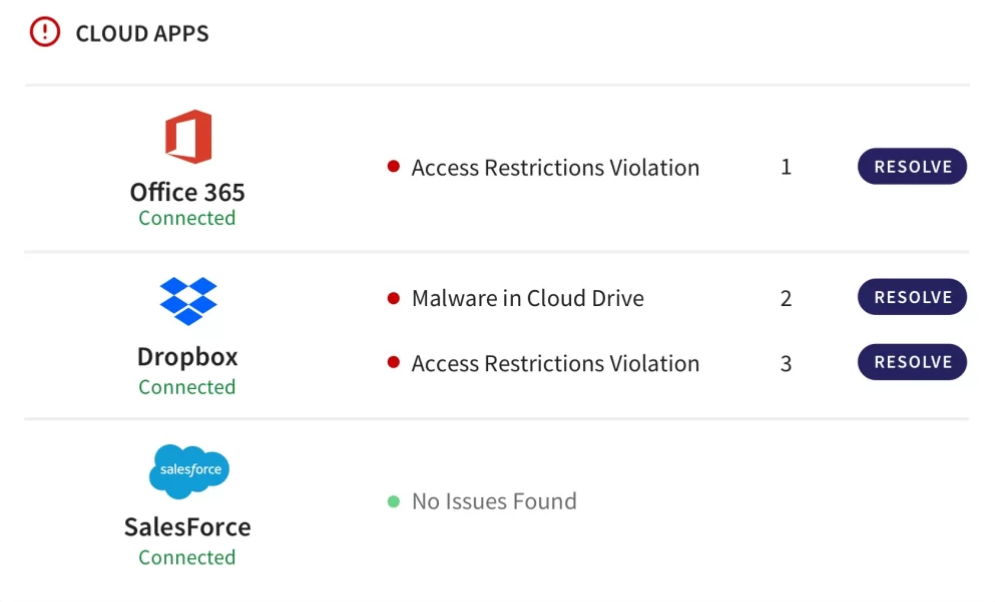
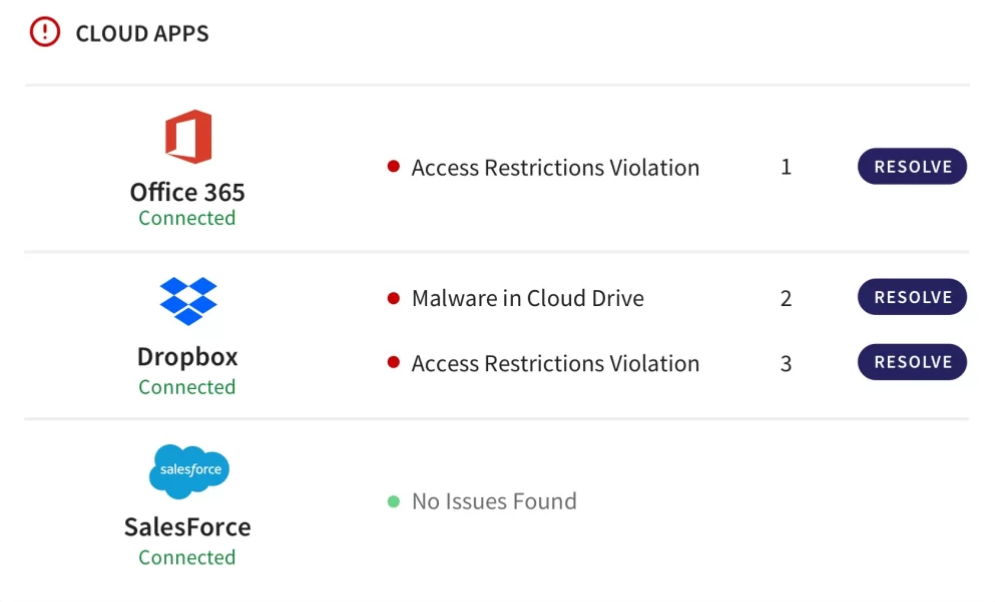
Cloud Security
Guard against malware in cloud drives and abnormal admin activity.
Mobile Device Management
Ensure your mobile devices remain threat free.
Inbound Gateway
Intercept inbound emails so only safe senders reach recipients.
Wifi Phishing
Prevent end users from connecting to suspicious wifi endpoints.
Secure Web Gateway
Filter web traffic to protect your business from malicious apps and sites.
Secure Message Encryption
Encrypt outbound emails so only recipients can view.
Cloud Security
Guard against malware in cloud drives and abnormal admin activity.
Mobile Device Management
Ensure your mobile devices remain threat free.
Endpoint Data Governance
Enforce data security policies on endpoints.
Zero Trust Network Access
Ensure access to apps, data, and services is secure.
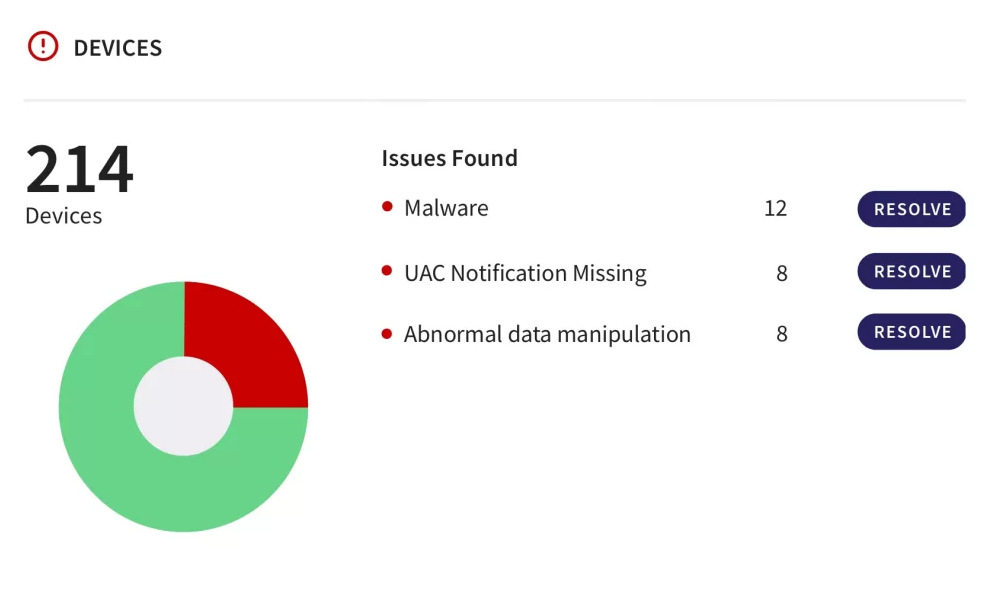
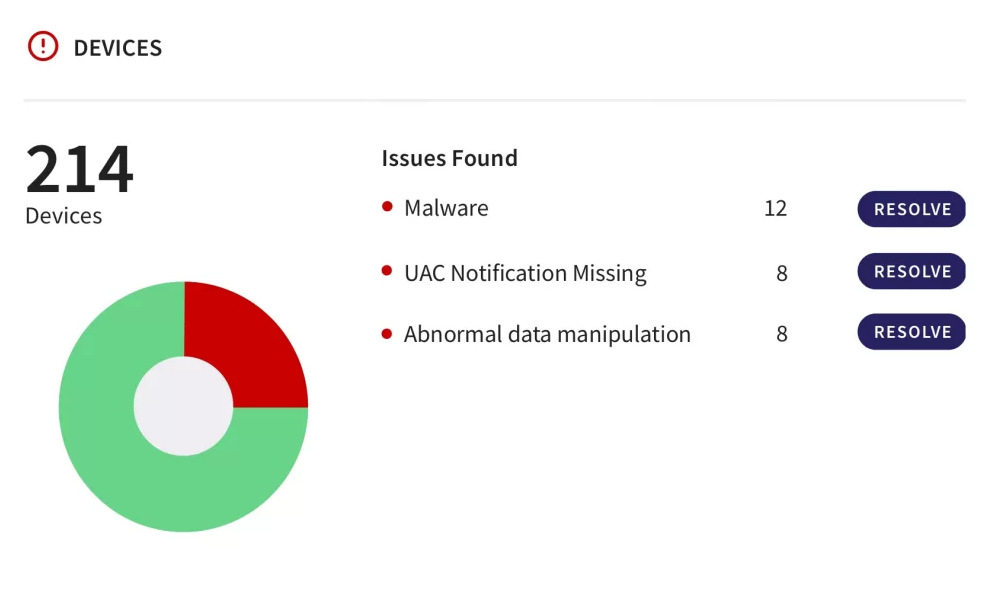
Endpoint Security
Set device posture, deploy NGAV, and allow/block processes.
Email Security
Protect against phishing, malware, and other fraudulent messages.
Network
Protect your network with cloud VPN, firewall, and remote office cluster.
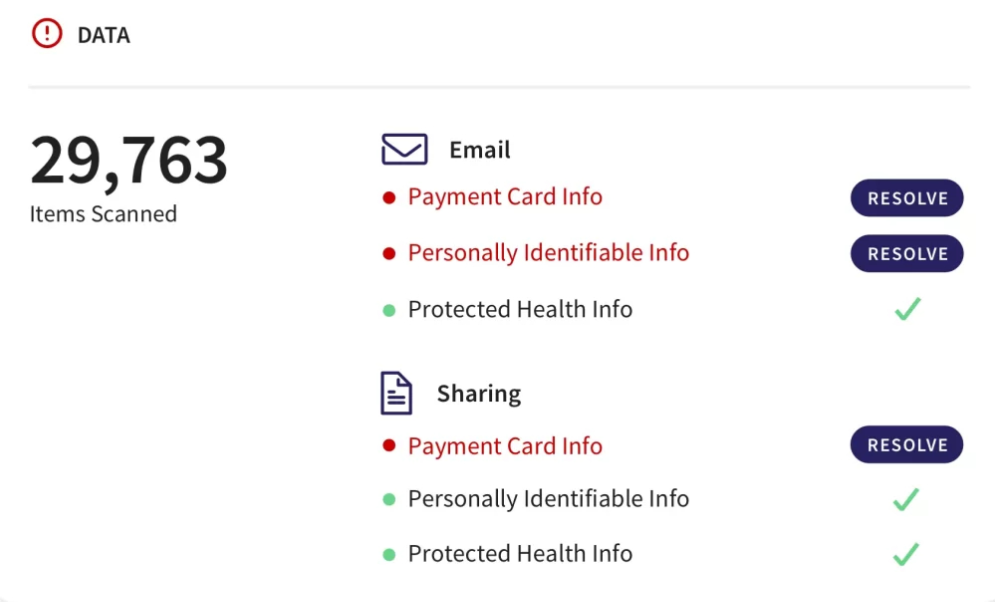
User Data Governance
Enforce secure handling of PII and other critical data.
Endpoint Data Governance
Enforce data security policies on endpoints.
Zero Trust Network Access
Ensure access to apps, data, and services is secure.
Endpoint Security
Set device posture, deploy NGAV, and allow/block processes.
Email Security
Protect against phishing, malware, and other fraudulent messages.
Network
Protect your network with cloud VPN, firewall, and remote office cluster.
User Data Governance
Enforce secure handling of PII and other critical data.
We use a strong defense mechanism to keep your users, devices, email, cloud apps, and data protected!
Featured Cyber Security Solutions for
Small and Medium Business

Setting the Standard In Cybersecurity - Here's What Sets Us Apart
| Kepler Safe | Others | |
|---|---|---|
| Budget | Cost Efficient | Expensive |
| Customer Support | 24/7 | Only on Weekdays (9 - 5) |
| Compliant | GDPR, HIPAA, and SOC 2 Compliant | Zero Compliances |
| Package | Single Solution | Different solution for Different Threats |
Recognized by Partners and Industry Leaders
Kepler Safe Understands Your Unique Industry Needs
Make Security Your Strong Suit with Kepler Safe!
Make Security Your Strong Suit with Kepler Safe!
Build a safe and compliant working environment for your users with our quick-to-install cyber security platform.
Stay Compliant with The Up to Date Security Regulations
The cyber threat intelligence mechanism that we use allows us to scan every file and email that passes through our network, identifying potential threats before they can cause harm.
Let Us Defend Your Inbox from Spam
Offering cutting-edge email security solutions where we use a vigilant AI technology that is specially designed to keep an eye out on your inbox for spam.
Keep Your Cloud Data Safe and Secure
Our cloud app protection takes the operational complexity and headaches out of cloud workload security, extending comprehensive protection to your public cloud assets.
Empowering You to Protect Your User Data
Protect the information of your users from insider threats, account hacking, and malicious activities by securing your endpoints with our symantec endpoint protection.
Pricing
Exclusive Low-Cost Cyber Security Package Just at $7/Month!
Starts at
$7
Monthly per module
FAQs About Kepler Safe and Its Capabilities
- Threat Intelligence
- Vulnerability Management
- Network Detection and Response (NDR)
- Endpoint Detection and Response (EDR)
- Behavioral Analytics
- Artificial Intelligence (AI)
- Conducting a risk assessment: Identifying potential threats and vulnerabilities in your technology platform, such as outdated software, unsecured networks, or weak passwords.
- Developing a cyber security plan: Create a plan that outlines the specific measures you will take to address these risks, such as implementing firewalls, antivirus software, and two-factor authentication.
- Integrating security into your platform: Implementing security controls into your technology platform, such as encryption, access controls, and intrusion detection systems.
- Training employees: Educate your employees on cybersecurity best practices, such as not clicking on suspicious links, using strong passwords, and reporting any security incidents.
- Regularly assessing and updating your security measures: Continuously monitoring your technology platform for potential threats and vulnerabilities, and making updates as necessary to keep your security measures up to date.
- Keep software up-to-date
- Use strong passwords
- Enable multi-factor authentication
- Use anti-virus and anti-malware software
- Educate employees
- Backup data regularly
WHAT THEY SAY ABOUT US
Testimonials
IT Director - Mid-Market G2Crowd Review
I'm so glad I did choose Kepler Safe for cyber security! Their team was incredibly knowledgeable and professional, and they took the time to explain everything to me in a language I could understand.
Seth B
Kepler Safe users since 2020
Overall, my experience with Kepler Safe has been positive, and I would recommend their services to anyone looking for a reliable cyber security solution.

SteganoAmor’s Steganographic Attacks Hit 320 Organizations Worldwide
Home The TA558 hacking group has initiated a fresh campaign, embedding malicious code within images through steganography to distribute diverse malware... read more
Protect Your Business: Understanding Cyberattacks and How Kepler Safe Can Help?
Home In today's digital age, cyberattacks have become a significant threat to businesses of all sizes. From data breaches to ransomware... read more

Cyberattack targets the systems of Omni Hotels, stealing reservations, money, and door locks
Home Omni Hotels & Resorts reported that a "disruption" on Friday caused its computer systems to go down. The American luxury... read more

Earth Krahang APT Targets Organizations Worldwide with Lesser-Known RESHELL Backdoor
Home The Earth Krahang APT group has emerged as a significant threat, employing sophisticated tactics to target organizations worldwide. Security researchers... read more

EquiLend Confirms Data Breach: Employees’ Information Stolen by Ransomware Gang
Home New York-based securities lending platform EquiLend Holdings has recently confirmed a data breach, notifying its employees that their data was... read more

Cyberattack Hits Change Healthcare Platform, BlackCat Ransomware Gang Claims Responsibility
Home A subsidiary of UnitedHealth Group (UHG), the Change Healthcare platform has suffered a significant outage, impacting more than 70,000 pharmacies... read more

Ransomware Attack Hits Critical Infrastructure Vendor PSI Software
Germany-based critical infrastructure software and logistics platforms vendor, PSI Software, has been hit by a devastating ransomware attack. read more

Integris Health Data Breach Exposes 2.4 Million Patients’ Personal Information
In a concerning development, Integris Health, Oklahoma's largest not-for-profit healthcare network, has reported a significant data breach affecting nearly 2.4... read more
